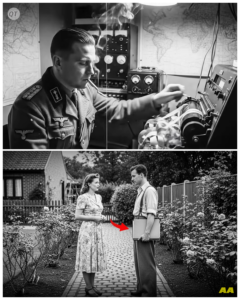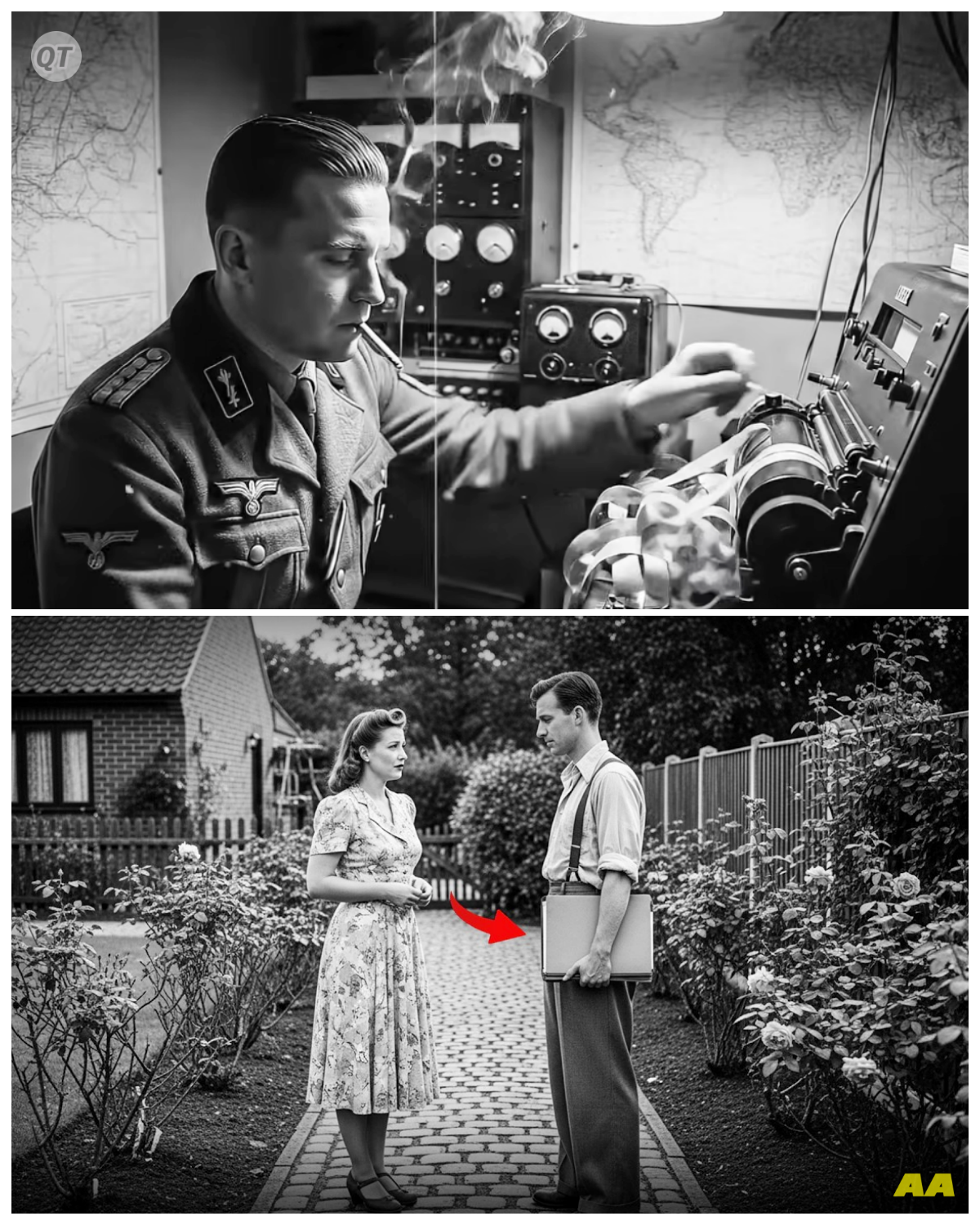
August 30th, 1941, 10:47 a.m.
A German radio operator in Athens sits at his Loren’s teleprinter machine, frustrated beyond measure.
He’s just spent 4 hours transmitting a 4,000 character encrypted message to Berlin.
Four grueling hours of perfect concentration.
And now Berlin radios back.
Message garbled.
Retransmit everything.
The operator makes a decision that will lose Germany the war.
Instead of resetting his encryption machine properly, he simply flips it back to the starting position and begins typing the exact same message again.
Same words, same order.
But here’s what makes this moment extraordinary.
The Loren’s machine creates slightly different encryption patterns each time, even from the same starting position.
Two identical messages, two different encryption keys transmitted within minutes of each other.
600 miles away, British wireless operators intercept both transmissions.
They have no idea what they’ve captured.
The encrypted gibberish sits in a pile with thousands of other intercepts, waiting for someone to notice the impossible coincidence.
And they might have never noticed it all, except for one thing.
A young codereaker’s girlfriend had just complained that he worked too much and never paid attention to detail anymore.
This is the story of how a relationship problem, a lazy German operator and Britain’s most secret facility broke the cipher that Hitler believed was absolutely unbreakable.
The Loren cipher, a code so complex that the Germans called it Gahheimshriber, the secret writer.
A machine so sophisticated it made Enigma look like a child’s toy.
By mid 1941, Britain had achieved something remarkable at Bletchley Park.
Alan Turing and his team had cracked the German Enigma machine.
Thousands of intercepted messages were being decoded daily, giving Allied commanders unprecedented insight into enemy operations.
But British intelligence officers noticed something disturbing.
Highlevel German military communications suddenly changed patterns in 1940.
Messages between Hitler’s headquarters and his army group commanders disappeared from Enigma intercepts entirely.
These weren’t tactical battlefield communications anymore.
These were strategic directives, orders for entire army groups, operational plans involving hundreds of thousands of troops.
The traffic was still there.
British wireless interception stations picked up the radio signals, but the encryption was completely different.
Not the familiar electrical rotors of Enigma machines, something else, something vastly more sophisticated.
Colonel John Tiltman, Britain’s foremost cryp analyst, examined the intercepts at the government code and cipher school.
The signals came from a teleprinter system, transmitting encrypted text at high speed.
The encryption changed with every single character.
Not every three or four letters like Enigma, but literally every individual character produced a different encryption pattern.
Tiltman calculated the mathematical possibilities.
An Enigma machine had approximately 159 quintilion possible settings.
this system.
The number was astronomical with 12 rotors instead of Enigma’s three or four and each rotor containing a different number of pins that could be set in binary positions, the theoretical key space exceeded 10 to the power of 19 possibilities.
To put that in perspective, if every person on Earth tried 1 million combinations per second, it would take longer than the age of the universe to test every possibility.
Intelligence estimates suggested Hitler used this system exclusively for communications with his top field marshals.
Operation Barbar Roa, the invasion of the Soviet Union, had been planned using these channels.
German strategy for North Africa flowed through this network.
The entire German high command coordinated through these unbreakable transmissions.
Britain was strategically blind at the highest level.
They could read tactical Enigma messages about individual units, but had no insight into Hitler’s grand strategic intentions.
And unlike Enigma machines, which the Poles had provided blueprints for before the war, British intelligence had absolutely no idea what this machine even looked like.
This is where that girlfriend complaint becomes critical to our story.
John Tiltman worked 16-hour days at Bletchley Park.
His social life had evaporated.
His girlfriend, whose name remains classified in British archives to this day, finally confronted him in late August 1941.
The complaint was simple, but cut deep.
You’re so absorbed in work that you’ve stopped noticing details in anything else.
You walk past me without seeing me.
You’ve become obsessive.
The accusation stung because Tiltman knew it was partially true, but it also sparked something in his analytical mind.
Was he missing details in his work because of exhaustion? Were there patterns in the intercepts that fresh eyes might catch? He made an unusual decision.
Instead of examining new intercepts himself, he began reviewing old material that had been filed away, specifically transmissions that seemed routine or unremarkable.
The rejected pile, the intercepts that junior analysts had deemed uninteresting.
On October 28th, 1941, nearly 2 months after they were intercepted, Tiltman found two transmissions from August 30th.
Both originated from the same German station in Athens.
Both transmitted to Berlin within a 30inute window.
Both were approximately 4,000 characters long.
The coincidence was striking.
German military protocol demanded different encryption settings for each message.
Two messages of identical length from the same sender at nearly the same time.
It violated every security procedure.
Tiltman laid out the intercepts side by side.
The encrypted text was completely different as expected, but something nagged at him.
He began comparing the patterns of the encryption itself, not trying to break it, just observing the structure.
Then he noticed something extraordinary.
At certain positions, both messages showed similar statistical anomalies.
The frequency of certain character patterns was too similar to be coincidental.
It suggested that underneath the different encryption, the underlying plain text message might be identical or nearly identical.
Tiltman knew what this meant.
A German operator had sent the same message twice using the same machine starting position but generating different encryption keys.
This was the cryptographic equivalent of finding the Rosetta Stone.
But what they didn’t know was just how lucky this moment truly was.
The specific error the German operator made would only expose the cipher’s weakness if the message was extremely long and if certain mathematical conditions aligned perfectly.
This combination would occur naturally only once in approximately every 10 million transmissions.
Tiltman assembled a team of six crypt analysts.
What they needed to perform was called a depth attack, a technique where two messages encrypted with related keys are compared to expose patterns in the encryption system itself.
The work was extraordinarily tedious.
Using just pencil, paper, and basic frequency analysis, the team began with a fundamental assumption.
German military messages followed predictable patterns.
They started with common German military abbreviations.
Numa for message number, KKR, which was German radio operators shortorthhand.
For 3 weeks, the team worked in 12-hour shifts.
They’d make an assumption about what a certain position in the plain text might be.
Use that to calculate what the encryption key at that position would need to be, then test if that key pattern worked for other positions.
Progress was agonizingly slow.
By November 15th, they had decrypted approximately 40 characters.
40 characters out of 4,000.
But those 40 characters confirmed they were on the right track.
The message was indeed German military communication discussing supply shipments to Raml’s Africa Corps.
Then on November 23rd, a breakthrough.
One of the younger crypt analysts, a Cambridge mathematics graduate named Peter Ericson, noticed that certain positions showed the encryption key repeating in predictable intervals.
Not the same key, but patterns in how the key changed.
intervals of 41 characters, then 31 characters, then 29 characters.
These were prime numbers.
The encryption machine used wheels with different numbers of positions, and they cycled at different rates.
The German engineers had deliberately chosen prime numbers to make the wheels cycle through their combinations as slowly as possible before repeating.
But here was the vulnerability.
Because the wheels moved at mathematically related rates, if you knew the wheel sizes and could identify where in their cycle they started, you could predict the entire key stream.
By December 10th, 1941, Tiltman’s team had reconstructed both complete messages, 4,000 characters of German highle communications sitting decrypted on a desk at Bletchley Park.
But the real prize wasn’t the message content.
It was the mathematical structure they had exposed.
They now understood the Loren machine’s logical architecture without ever having seen the physical device.
The machine used 12 wheels.
Five were key wheels that created one pattern.
Five were C wheels creating another pattern.
And two were motor wheels controlling when the C wheels moved.
The encryption at each position was created by combining these patterns using binary addition.
Understanding the machine’s logic and actually breaking messages in real time were entirely different challenges.
What Tiltman had accomplished took six weeks of intensive work for just one message.
German high command sent dozens of these messages daily.
Britain needed an industrial solution.
This is where one of history’s most brilliant engineers enters the story.
William Thomas Tut, a chemistry graduate student who’d been recruited to Bletchley Park in 1941, not for his mathematical genius, but because he was good at crossword puzzles and word games.
Tut took Tiltman’s work and asked a question nobody else had considered.
What if we don’t try to decrypt the message at all? What if we just figure out the machine’s wheel settings and let that tell us the key? It was a radical inversion of the problem.
Instead of attacking the cipher, attack the machine’s configuration.
If you could determine the starting positions and pin patterns of all 12 wheels, generating the keystream became trivial.
Then decryption was simple binary mathematics.
Tut de developed a statistical method based on character frequency analysis.
German military language used certain letters far more frequently than others.
The letter E appeared roughly 17% of the time.
By analyzing the encrypted output and applying statistical tests, Tut could make probabilistic guesses about wheel positions.
However, the real breakthrough came when they finally solved that problem.
Max Newman, a mathematics professor working at Bletchley Park, recognized that Tut’s method required performing the same calculations thousands of times with slightly different parameters.
This wasn’t a job for humans.
This was a job for a machine.
Newman approached Tommy Flowers, an engineer from the post office research station at Dallas Hill in London.
Flowers was an expert in telephone switching systems and had pioneered work with electronic valves, what Americans called vacuum tubes.
Newman explained the requirement.
A machine that could read encrypted teleprinter tape at high speed, perform binary logical operations, comparing the tape to generated key patterns, count specific character combinations, and do this fast enough to test multiple wheel configurations in reasonable time.
Flowers listened, then said something that shocked everyone in the room.
I can build that.
It’ll use electronics, not mechanical relays.
It’ll process 5,000 characters per second, and I’ll have a prototype ready in 11 months.
Every engineer in Britain had told Newman that such a machine was impossible.
Electronic valves were unreliable.
They burned out constantly.
Building a machine with hundreds of valves would mean constant breakdowns.
The calculations required were too complex for electronic circuits.
Flowers disagreed on every point.
He’d been experimenting with valve technology for telephone exchanges.
He knew that valves failed primarily during power on when the thermal stress stressed the components.
His solution was elegant.
Never turn the machine off.
Keep the valves at constant temperature and they’d run reliably for months.
Tommy Flowers returned to Dallas Hill and assembled a team of engineers.
Working with a budget so limited that Flowers partially funded the project from his own pocket, they began building what would become known as Colossus.
The machine was enormous.
It stood 7 ft high, 16 ft wide, and 11 ft deep.
It contained 1,500 electronic valves in the first version, later increased to 2400 in subsequent models.
For context, most contemporary electronic devices used fewer than 20 valves.
The engineering challenges were extraordinary.
The machine needed to read paper tape moving at 30 mph without tearing it.
Flowers developed a specialized sprocket system that pulled the tape through five reading heads simultaneously using photoelectric cells to detect the punched holes that represented encrypted characters.
Each valve circuit performed binary logic operations and or and exor gates that compared the input tape to internally generated patterns.
The machine would count specific combinations and display the results on neon indicator panels.
Operators could then adjust the generated pattern settings and run another test.
The first Colossus became operational at Bletchley Park on February 5th, 1944.
The timing was critical.
D-Day was 4 months away.
Allied commanders desperately needed intelligence about German defensive preparations in France.
The machine’s first operational task was decrypting a message intercepted on February 4th from Field Marshal Ger von Runstet’s headquarters.
The message was 5,000 characters long.
Manual methods would take weeks to break.
Colossus processed it in 4 hours.
The decrypted message revealed German assessments of potential Allied invasion beaches.
It confirmed that Hitler believed the invasion would come at Pika, not Normandy.
This intelligence directly influenced Allied deception operations and the ultimate success of D-Day.
By June 1944, 10 Colossus machines operated around the clock at Bletchley Park.
Each machine bore a feminine name, Colossus 1, Colossus 2, and so forth.
The machines worked in coordination with different Colossi testing different wheel setting combinations for the same message, dramatically reducing the time to solution.
The Colossus operators were predominantly women from the Women’s Royal Naval Service, known as Rens.
They received minimal explanation about what the machines did or why.
Their training focused entirely on operating procedures, how to load tapes, set switches according to written instructions, record results, and maintain the equipment.
Security protocols forbade them from discussing their work with anyone, including other rens working different shifts.
The machines proved astonishingly reliable.
Flower’s prediction about continuous operation was correct.
Valves rarely failed when kept at constant temperature.
When failures did occur, the modular design allowed engineers to swap circuit boards in minutes rather than hours.
But here’s what makes this achievement truly remarkable.
Colossus wasn’t just the first electronic programmable computer used in warfare.
It was arguably the first programmable digital electronic computer, period.
The Aniac, often credited as the first computer, didn’t become operational until 1945, but Colossus remained classified for decades.
So, its place in computer history was hidden.
The machine used conditional logic, performed program sequences of operations, and could be reconfigured for different tasks by changing switch settings and plug configurations.
By modern definitions, it was a computer.
Yet, Tommy Flowers never received public recognition during his lifetime because the Official Secrets Act forbade him from revealing what he’d built.
The intelligence gained from breaking Lorent intercepts, codenamed Tunny by the British, provided unprecedented strategic advantage.
Unlike Enigma, which revealed tactical and operational information, Lorent messages came directly from Hitler’s Supreme Headquarters to army group commanders.
These were strategic directives affecting entire theaters of war.
General Dwight Eisenhower later stated that intelligence from Bletchley Park shortened the European War by approximately 2 years.
While this assessment included all coderebreaking efforts, historians now recognize that Laurance decrypts specifically provided intelligence that Enigma could never access.
For example, in July 1943, Laurance Decrypts revealed Hitler’s complete operational plan for the Battle of Kursk, the largest tank battle in history.
Soviet commanders, who received carefully sanitized intelligence from British sources, positioned their defenses with perfect knowledge of German attack axes and timings.
The resulting German defeat marked the permanent shift of initiative on the Eastern Front.
Throughout 1944 and early 1945, Lorent decrypts tracked German military dispositions across Europe with remarkable precision.
Allied commanders knew division locations, supply status, and strategic reserves with detail that seemed almost supernatural.
German generals later expressed bewilderment at how Allied forces repeatedly appeared exactly where they were weakest.
By war’s end, 10 Colossus machines operated at Bletchley Park.
The British had processed tens of thousands of intercepted Lorent messages, creating an intelligence advantage that German commanders never understood they were conceding.
What makes this story particularly poignant is how thoroughly it was hidden after the war.
In late 1945, Winston Churchill personally ordered the destruction of most Colossus machines.
Eight of the 10 were dismantled and destroyed.
The remaining two were moved to the government communications headquarters where they continued classified work until 1960.
Every person who worked on Loren’s codereaking signed the Official Secrets Act.
They were forbidden from discussing their work, not just with the public, but with their own families.
Tommy Flowers couldn’t explain why he’d spent 2 years of his life building mysterious machines.
The Rens who operated Colossus couldn’t tell their children what they’d done during the war.
John Tiltman died in 1982.
His obituaries mentioned his work at Bletchley Park, but couldn’t specify his actual achievements.
William Tut lived until 1992, spending most of his life as a mathematics professor in Canada.
His groundbreaking cryp analysis remained classified until the 1990s, long after similar work would have earned him international recognition.
Tommy Flowers struggled financially after the war.
He’d spent over £1,000 of personal money building Colossus prototypes, equivalent to roughly £50,000 today.
The government initially refused to reimburse him because he couldn’t document what the money was spent on without violating secrecy laws.
He eventually received £300 compensation.
The story only became public in 2000 when British intelligence finally declassified the Loren’s codereing operation.
By then, most of the key figures were dead.
A rebuilt Colossus now operates at the National Museum of Computing at Bletchley Park.
constructed from photographs and surviving technical documentation.
The principles that broke the Loren cipher remain fundamental to modern cryp analysis.
Statistical analysis of encrypted data, automated pattern recognition, and using computational power to test multiple hypotheses simultaneously.
These form the basis of contemporary codereing.
But perhaps more importantly, this story illustrates a truth about complex problemolving.
Breakthroughs often come from unexpected places.
A girlfriend’s complaint about inattentiveness led Tiltman to review old intercepts with fresh eyes.
A German operator’s laziness created a vulnerability in a theoretically unbreakable system.
An engineer ignored expert consensus about valve reliability and built a machine everyone claimed was impossible.
The Loren cipher was mathematically stronger than modern encryption systems still used today.
If that German operator in Athens had simply reset his machine properly on August 30th, 1941, the cipher might never have been broken.
The war’s outcome could have been dramatically different.
Hundreds of thousands of lives potentially hung on one person’s decision to take a shortcut.
This is what makes military history fascinating when you focus on technical problem solving rather than battles.
The outcome of World War II wasn’t determined solely by generals and soldiers.
It was also decided by mathematicians with pencil and paper, engineers building impossible machines, and the random intersection of human error with human brilliance.
If you found this story compelling, consider this.
The British weren’t the only ones breaking supposedly unbreakable codes during World War II.
American cryp analysists faced an entirely different challenge in the Pacific.
A Japanese cipher machine called Purple that encrypted diplomatic communications using a principle so unusual that nobody initially believed the machine could physically exist.
That story involves a language barrier, rotating telephone switches, and a breakthrough that came from analyzing not what the machine encrypted, but the physical sounds it made during encryption.
But that’s a story for another time.
[snorts] If you want to see more technical problem-solving stories from military history, the engineering, the innovation, the human ingenuity under impossible circumstances, subscribe to this channel.
Hit that notification bell and leave a comment telling me what type of wartime technical problem you’d like to see explored next.
Communication systems, engineering challenges, prison camp innovations.
The next story is already being researched, and I promise it’s equally remarkable.
News
How 30 Japanese ships and 430 planes were destroyed in one day-ZZ
The day Japan’s Navy died. June 19th, 1944. The Philippine Sea. Vice Admiral Jiso Ozawa stands on the bridge of Japan’s newest aircraft carrier, Taiho, watching the sun rise over the Pacific. Around him, nine carriers carry over 400 aircraft. Behind him, battleships and cruisers form the most powerful fleet Japan has assembled since midway […]
How 30 Japanese ships and 430 planes were destroyed in one day-ZZ – Part 2
They remembered the supremely skilled elite aviators who had swept victoriously through the Pacific in 1941 and completely failed to recognize that those exceptional men were dead, replaced by undertrained noviceses flying into a technological trap their commanders did not understand and had not prepared them to survive. The Americans that Ozawa’s pilots faced in […]
“Clint Eastwood’s Dark Revelation: ‘He Was The Devil!’—A Shocking Tale of Fear and Betrayal!” -ZZ In a sensational twist that has left the entertainment world buzzing, Clint Eastwood breaks his silence with a chilling statement: “He was the devil!” As the actor peels back the layers of his past, a haunting narrative of fear, betrayal, and darkness emerges. Who is this enigmatic figure that has haunted Eastwood for so long, and what shocking truths will come to light? Get ready for a thrilling ride through the dark corners of fame and fortune!
Clint Eastwood Breaks Silence: “He Was The Devil” In the realm of Hollywood, where legends are born and stories of triumph and tragedy intertwine, few figures stand as tall as Clint Eastwood. Known for his rugged charm and no-nonsense attitude, Eastwood has carved out a legacy as one of the most iconic actors and directors […]
“Behind Closed Doors: The Disturbing Truth About Princess Beatrice’s Husband!” -ZZ In a jaw-dropping exposé, the truth about Princess Beatrice’s husband has finally emerged, and it’s a narrative fraught with scandal and heartbreak. As the royal family braces for impact, fans are left stunned by the shocking secrets that threaten to unravel the very essence of their glamorous lives. Will this revelation lead to a royal rift, or can love conquer all? Join us as we dive deep into this sensational saga of love, betrayal, and royal intrigue!
The Shocking Truth About Princess Beatrice’s Husband: A Scandal Unveiled In the world of royalty, where every move is scrutinized and every relationship analyzed, few stories captivate the public’s imagination quite like that of Princess Beatrice and her husband, Edoardo Mapelli Mozzi. On the surface, Mozzi appeared to be the perfect match for the princess—an […]
“The Dark Side of Royalty: Princess Beatrice’s Husband’s Shocking Truth Revealed!” -ZZ Hold onto your tiaras, folks! The truth about Princess Beatrice’s husband has finally emerged, and it’s a scandal that could rock the very foundations of the royal family. With revelations that paint a picture of deceit and turmoil, this story is not for the faint-hearted. As the royal couple faces an unexpected crisis, the question remains: can love survive when the truth is anything but good? Dive into this sensational tale of betrayal and intrigue!
Alan Jackson’s Heartbreaking Diagnosis: A Farewell to a Country Legend? At 67, Alan Jackson stands as a towering figure in the world of country music. With a career that spans decades, he has woven the fabric of American music with his soulful voice and heartfelt lyrics. From the moment he burst onto the scene with […]
The Nurse Thought It Was Just a Reflection in the Glass Until She Turned and Claimed She Saw Carlo Acutis Standing Quietly by the Bed and What Happened Next Left Her Questioning Everything She Believed About Reality -KK It began as a routine night shift, the kind filled with silence and small, predictable movements, but in a single moment that calm shattered, because what she first dismissed as a trick of light quickly became something she could not explain, something that stayed with her long after the room fell silent again. The full story is in the comments below. – Part 2
Moreover, the information about Emma’s dress was never digitally documented. It existed only in my memory and in physical photographs that no one but me had seen for 8 years. What is your professional assessment as a nurse trained in evidence-based medicine of how Carlo obtained this knowledge? The only explanation consistent with the evidence […]
End of content
No more pages to load