Investigators in Arizona are bringing in some new tools in the search for Nancy Guthrie today in the race to identify the mass and armed individual captured on NY’s doorbell camera.
They now have a forensic height camera involved.
1:47 in the morning, 2:28 in the morning, 41 minutes apart.
You have been following this case.
You know who Nancy Guthrie is.
You know her daughter, Savannah.
You know the neighborhood in the Catalina foothills.
You have seen the masked figure.
You have heard about the Bitcoin ransom.
You have followed the dead ends, the searches, the reward, the heartbreak.
You have been here from the beginning.
And you know more about this case than most people in America.
So today we are not going to rehash what you already know.
Today we are going to do something different.
Today we are going to take those 41 minutes 147 to 228 and we are going to put them under a microscope.
We are going to slow everything down.
We are going to go minute by minute, detail by detail, and we are going to ask the questions that nobody else is asking out loud.
Because here is the truth.
Those 41 minutes are the entire case.
Everything that matters, every answer this investigation needs, every secret someone is keeping exists somewhere inside those 41 minutes.
And nobody, not law enforcement, not the media, not the FBI, has publicly explained what actually happened inside that window.
I am going to try.
Welcome to Crime View.
If you have been with us through all 16 episodes on this case, you already know we do not do shallow coverage here.
Today is no different.
Today, we go deeper than we have ever gone.
So stay with me all the way through because I promise you this video is not the same thing you have heard 16 times before.
And if you have not subscribed to Crime View yet, right now is a great time to do it because this kind of in-depth analysis is what we do every single week.
Let us begin.
Here is the thing about those 41 minutes that has been bothering investigators, analysts, former law enforcement professionals, and frankly anyone who has thought carefully about this case.
41 minutes is a very strange number.
Think about it from a pure logistics standpoint.
147 is when the camera goes dark.
228 is when the pacemaker stops sinking.
41 minutes between those two events.
And the question nobody has answered cleanly is what exactly fills those 41 minutes? Because the answer to that question tells you almost everything about what kind of operation this was, how many people were involved, and whether or not whoever did this knew exactly what they were doing.
Let us break it down the way an investigator would.
At 147, the masked figure deliberately disconnects the doorbell camera.
That is confirmed.
Now, think about what that tells us about the mindset of the person doing it.
They are not panicking.
They are not rushing.
Disconnecting a camera at 1:47 in the morning in the dark at the front door of a house takes a moment of focus.
You have to reach up.
You have to locate the device.
And according to FBI Director Cash Patel, the individual first tried light taps to knock the camera off before using foliage from a potted plant on the porch to cover the lens.
Light taps.
Foliage.
This person tried two different methods to neutralize that camera.
That is not the behavior of someone who is improvising.
That is the behavior of someone who had a plan, encountered a minor obstacle when the first method did not work immediately, and pivoted to a backup plan without missing a beat.
So, at 147, we have a calm, deliberate, masked individual standing at NY’s front door, systematically working to eliminate the only exterior surveillance on the property.
Fine.
That is minute 1 of the 41.
What happens next? Between 1:47 and 212, there is a gap in the confirmed timeline.
We know that at 212, additional motion is detected, presumably by the same doorbell camera system or nearby sensors.
That is 25 minutes between the camera tampering and the next confirmed motion detection.
25 minutes of silence in the documented record.
That is a long time.
What is happening during those 25 minutes? There are three possibilities worth considering seriously.
Possibility one, the person was already inside the house before 147 and the camera disabling at 147 was actually one of the last steps before the operation concluded, not one of the first.
That would mean the intruder had already entered through a different entry point.
Perhaps a back door, a window, an unlocked secondary entrance, and the camera was disabled as part of covering an exit, not preparing an entry.
Possibility two, the person entered the house immediately after disabling the camera at 1:47.
And the 25-minute gap represents the time spent inside the house locating Nancy, subduing her, and preparing to move her.
Possibility three, the person waited outside for 25 minutes after disabling the camera, either waiting for a signal, a vehicle, a partner, or a specific window of time.
Law enforcement has not publicly clarified which of these scenarios the evidence supports.
And that is a problem because which scenario is true dramatically changes the picture of what happened inside that home.
Then at 212, motion is detected again.
That could be the figure moving back toward the door with Nancy.
It could be additional activity from a second person.
It could be Nancy herself being moved.
We do not know.
What we know is that 16 minutes after that 212 motion detection, at exactly 228, the pacemaker misses its scheduled transmission.
16 minutes.
Between 212 and 228, 16 more minutes of activity, motion, something inside or around Nancy Guthri’s home, and then silence.
The pacemaker goes quiet and Nancy is gone.
41 minutes total, 147 to 228.
That is the entire known operational window of whatever happened in that house.
And that window tells us something important that I do not think has been fully explored in public coverage of this case.
41 minutes is a relatively short operational window for an abduction of an elderly person with limited mobility.
This was not a long drawn out siege.
This was not a situation where someone broke in and spent hours inside.
In and out, camera to pacemaker 41 minutes.
That level of efficiency suggests planning.
It suggests a rehearsed sequence of events.
It suggests that whoever was inside that house on the night of January 31st into February 1st had thought through every step in advance.
And yet at the same time, if this was such a wellplanned operation, why did the Google Nest cloud backup work? Why did the footage get uploaded before the camera was fully neutralized? A truly sophisticated criminal operation in 2026 would know that cloud connected devices upload continuously, not just when they are actively being viewed.
A truly sophisticated operation would have disabled the Wi-Fi router first, cutting off the camera’s upload connection before physically tampering with the device.
Whoever did this either did not know about the cloud backup function or they knew and could not get to the router.
That is a gap in their planning, a significant one, and it gave the FBI the footage that America has now seen.
So, what we have is someone who was sophisticated enough to plan a 41-minute abduction of an 84year-old woman in a monitored home, but not sophisticated enough to kill the internet connection before tampering with a camera.
That combination tells us something about who we might be looking for.
Not a career criminal with deep technical knowledge, but not a complete amateur either.
Someone in the middle, someone who knew some things and did not know others.
What the pacemaker actually tells us.
I want to spend real time on the pacemaker because most coverage of this element has been surface level.
People mention it, note that it stopped transmitting, and move on.
But when you dig into the medical and technical specifics of what pacemakers actually do, what data they actually collect, and what the miss at 228 actually might mean, the story gets much more interesting.
Most people think of a pacemaker as a simple device that keeps the heart beating.
That is true, but it understates what modern pacemakers are capable of.
A current generation pacemaker is essentially a computer implanted in your chest.
It monitors your heart rhythm continuously, 24 hours a day, 7 days a week.
It records every single heartbeat.
It logs the time, the rate, whether the beat was natural or pacemaker initiated.
It tracks episodes of unusual heart activity.
And in many models, it stores weeks or months worth of this data internally, transmitting summaries to an app on the patient’s smartphone, either nightly or during scheduled check-in windows.
NY’s pacemaker app was on her phone.
Her phone was left behind in the house.
Based on the reporting we have, the pacemaker was designed to transmit its nightly data to the phone app during a scheduled window that included 2:28 in the morning.
At 2:28, that transmission was missed.
The last confirmed data packet came just before that time stamp.
Now, here is the critical medical detail.
Dr.
Jonathan Reiner, one of the most respected cardiologists in America and the former personal physician to former vice president Dick Cheney, spoke on CNN about exactly this.
He noted that if Nancy was involved in a physical confrontation around 2 in the morning, her heart rate would almost certainly have elevated significantly.
Fear alone can spike heart rate dramatically, even in someone with a pacemaker.
A pacemaker does not suppress the heart’s natural response to adrenaline.
It manages rhythm, but if the heart starts beating faster due to stress or fear or physical exertion, the pacemaker detects that elevated rate and in many cases logs it as a notable event.
What Dr.
Reiner was suggesting is that the final data transmission from NY’s pacemaker, the last packet that went through before 228, may contain a record of her heart activity during those final moments.
If there was a struggle, if she was confronted or grabbed or frightened, that data may show it.
A spike in heart rate, an episode of irregular rhythm triggered by extreme stress, the pacemaker would have recorded it.
So why does this matter? Because that data is evidence.
It is biological, medical, timestamped evidence of what NY’s body was experiencing in the minutes before she disappeared.
The FBI obtained that data.
We know they did because they contacted the pacemaker manufacturer, requested all records, and reportedly deployed signal sniffers to try to locate the device, but they have not publicly disclosed what that data shows.
I want to pose a question, and I want you to really think about it with me.
If the pacemaker data showed nothing unusual, if NY’s heart rate was normal and steady right up until the transmission missed, what would that tell us? It would tell us that she was not in a state of physical stress or fear.
A normal steady heart rate at 2:28 in the morning in a woman who was supposedly being abducted from her home would be medically inconsistent with a violent kidnapping.
It would suggest she was either unconscious, deeply sedated, or perhaps not in her home at all at that point.
On the other hand, if the pacemaker data showed a sharp spike in heart rate in the minutes leading up to 228, that would be consistent with fear, confrontation, physical exertion, exactly what you would expect from someone being taken against their will.
That data would corroborate the kidnapping theory.
The FBI has this data.
Law enforcement has this data.
And they have said nothing publicly about what it shows.
That silence, that very deliberate silence is one of the most intriguing elements of this entire case to me.
It is entirely possible, even likely, that they are withholding that information strategically to preserve the integrity of an ongoing investigation.
But it is also worth noting what information silence can inadvertently communicate.
There is one more detail about the pacemaker that has received almost no attention in mainstream coverage and I think it deserves our focus.
The signal sniffers.
When law enforcement deployed what they called signal sniffers in the search for Nancy, they were specifically looking for the Bluetooth signal emitted by her pacemaker.
Modern pacemakers emit a low energy Bluetooth signal almost continuously when they are active.
This signal is normally only detected by the paired smartphone app when they are in close range.
But the FBI has access to specialized equipment that can detect Bluetooth signals at greater distances than a standard phone.
The hope was that if Nancy was alive and within a certain geographic radius, her pacemaker would give away her location.
As of April 2026, no confirmed detection of NY’s pacemaker signal has been publicly reported.
No found signal does not necessarily mean Nancy is dead.
It could mean she is being held somewhere beyond the detection range of the equipment that was deployed.
It could mean she is in a location with significant physical shielding like a concrete basement or a metal structure that disrupts the signal.
It could mean she was moved across the border into Mexico where domestic US law enforcement signal detection technology cannot easily operate.
But it also could mean the device is no longer active.
A pacemaker battery typically lasts between 7 and 15 years depending on the model and how frequently it fires.
NY’s pacemaker battery would not have died in 2 months.
If the signal is not detectable, it is not because the battery ran out.
So either the device is being physically shielded or Nancy is beyond the range of deployment or something else has happened.
This is the part of the case that is the hardest to say out loud and I want to acknowledge that hardness.
But this is Crime View and our commitment is to look at every angle honestly.
The camera footage.
Five things people missed.
When the FBI released the doorbell camera footage on February 10th, most of the coverage focused on the broad physical description of the suspect.
5’9 to 510, average build, black mustache, dark clothing, gloves, Ozark Trail backpack, gun in a front holster.
That is what got reported.
But when you actually watch the footage carefully or when you read the detailed FBI bulletin, there are several specific details in that footage that most coverage glossed over and I want to walk through each one of them.
The first detail is the holster position.
The weapon the suspect is carrying is described as being in a holster positioned near the front of the lower body.
That is not a typical carry position.
Standard law enforcement and military carry positions are on the hip, either strong side or crossdraw.
A front holster, particularly a low front position, is associated with specific tactical training styles or with individuals who have had formal training in close quarters operations.
It is unusual.
It is notable.
And in combination with the calm, deliberate behavior of disconnecting the camera, it paints a picture of someone with some level of tactical training or at minimum tactical awareness.
The second detail is the backpack.
The Ozark Trail Hiker Pack is a 25 L capacity hiking backpack sold primarily at Walmart.
It is inexpensive.
It is common.
It does not stand out.
The choice of an inexpensive, easily available, untraceable backpack is a deliberate choice.
It is the kind of choice someone makes when they want their equipment to be as generic as possible.
No distinctive brand, no unique coloring.
Nothing that would stand out to anyone who might see them in the neighborhood before or after the operation.
But here is the thing about that backpack that nobody has talked about enough.
25 L is a specific capacity, and 25 L tells us something about what was in it.
A 25 L pack can hold approximately a small change of clothing, basic tools, food, and water for several hours, and potentially restraint materials.
It is not a large pack.
It is not a go bag for a multi-day disappearance.
It is a short operation pack.
Whatever was in that bag was intended for use during the immediate operation, not for an extended journey.
The kidnapper or kidnappers came with a relatively small kit.
That suggests either the operation was planned to be very short and focused or there was a larger vehicle with additional supplies very close by.
The third detail is the attempt with foliage.
The suspect first tries to physically remove or disable the camera with light taps.
When that does not immediately work, they reach for a potted plant on the porch and use foliage to cover the lens.
This is a pivot, a realtime adjustment.
But it also tells us that the suspect had not rehearsed this specific step in full detail.
A fully rehearsed operation would have had a more decisive method of camera neutralization from the start.
The foliage improvisation is the first hint that this was planned but not perfectly executed.
There are seams in the plan and where there are seams there is evidence.
The fourth detail is what the footage does not show.
We have the footage from the doorbell camera.
What we do not have at least publicly is footage from any other cameras in the area.
The Catalina foothills neighborhood is a reasonably affluent area.
Affluent neighborhoods typically have multiple points of surveillance coverage.
Not just individual doorbell cameras, but community cameras, vehicles with dash cameras parked on streets, cameras at nearby businesses or intersections.
In a neighborhoodwide investigation with the full force of the FBI behind it, canvas of surrounding surveillance footage should have produced additional sightings of this individual either approaching the property or leaving it.
The near complete absence of additional surveillance footage in public reporting is strange.
Either it does not exist, the escape route avoided all secondary cameras, which would again imply careful prior planning and surveillance of the neighborhood, or additional footage exists, but has not been released publicly.
The fifth detail is the time itself, 1:47 in the morning.
This is a very specific time choice for this type of operation.
Not midnight, not 2:00 a.
m.
or 3:00 a.
m.
, 1:47.
The specificity of that timing might mean nothing.
It might be the time that the person arrived naturally based on travel time and other factors, but it might also reflect someone who had done surveillance of this neighborhood and knew specifically that the combination of reduced ambient noise and the particular pattern of any remaining nighttime activity in this neighborhood made 1:47 the optimal window.
3:00 in the morning is actually the time when most people who have been awoken by a noise decide it was nothing and go back to sleep.
1:47 falls right in the middle of the deepest sleep window for most people who go to bed before midnight.
The timing may be calculated.
The ransom notes reading between the lines.
You know about the ransom notes.
CBS got one.
TMZ got one or more.
Bitcoin was demanded.
$6 million.
a deadline of February 9th at 5:00 in the afternoon and then the deadline passed.
But let us read between the lines on these notes because the details of how the ransom communication was structured tell us something very important about the psychology and strategic thinking of whoever wrote them.
First, the choice to send ransom notes to media organizations rather than directly to the family is highly unusual.
In the vast majority of kidnapping cases, ransom communication goes directly to the family through text messages, through letters to the family’s home, through phone calls.
The family is the party who has the money and the motivation to pay.
Sending notes to CBS and TMZ bypasses the family entirely and essentially makes the ransom demand a public performance.
The kidnapper or kidnappers went to the media.
Why? There are a few possible explanations.
One is intimidation.
By going public with the demand, the abductors make the entire situation visible to law enforcement in a way that might pressure the family to act quickly before investigators have time to establish a response strategy.
Another possibility is leverage.
With the media amplifying the ransom demand, the family is publicly aware of it and publicly on the hook.
the eyes of the nation are now watching to see what the Guthri do.
That is enormous psychological pressure.
A third possibility is that going to the media was a way of establishing that the abductors were serious and in control, a public demonstration of power.
The fact that the note to TMZ contained specific details about what Nancy was wearing on the night she disappeared is the detail that has haunted this case from the very beginning.
Think about that detail carefully.
Not just what it tells us in isolation, but what it tells us in combination with everything else.
Nancy was dropped off at her home at 9:50 on the evening of January 31st.
Between 9:50 and the camera going dark at 1:47, roughly 4 hours pass.
4 hours during which presumably Nancy was inside her home preparing for bed.
the detail in the ransom note about her clothing.
Was it what she was wearing when she was dropped off? Was it what she was wearing when she was found inside the house? Was it what she was wearing when she was taken? If the note describes what Nancy was wearing when she arrived home that evening, it could mean the notewriter was watching her when Toamaso dropped her off, watching from the street, from a parked vehicle, from somewhere with a line of sight to the garage as it closed.
If the note describes what she was wearing when she was taken inside her house, it means the notwriter had direct personal access to information about what happened inside the home during those 41 minutes.
Both options are deeply troubling.
One requires external surveillance.
The other requires internal access to information.
The content of one of the later notes allegedly claimed that Nancy was alive, that she was scared, that she was aware of the demands being made, and then this will be their only communication.
Their only communication.
That phrase is important.
It signals finality.
It signals that the abductors do not intend to negotiate back and forth.
Pay or do not pay, those are your options.
It also signals a desire to control the entire timeline and process.
No ongoing dialogue, no opportunity for law enforcement to trace communication patterns.
One message, either you comply or you do not.
And then the deadline of February 9th came and went.
Law enforcement has never confirmed publicly whether any payment was made or attempted.
The family has never confirmed or denied payment.
This is completely understandable, by the way.
If a payment was made or attempted, disclosing that publicly could jeopardize any ongoing effort to use the transaction to trace the recipients.
If no payment was made, disclosing that could, at least in theory, affect NY’s safety.
So, the silence from the family on this point is not suspicious.
It is responsible.
But that silence also means we do not know what happened on February 9th at 5:00 in the afternoon.
We do not know if that deadline meant anything.
We do not know if it passed without consequence or if it marked a turning point.
And in a case with this many open questions, every unanswered question adds weight to the pile.
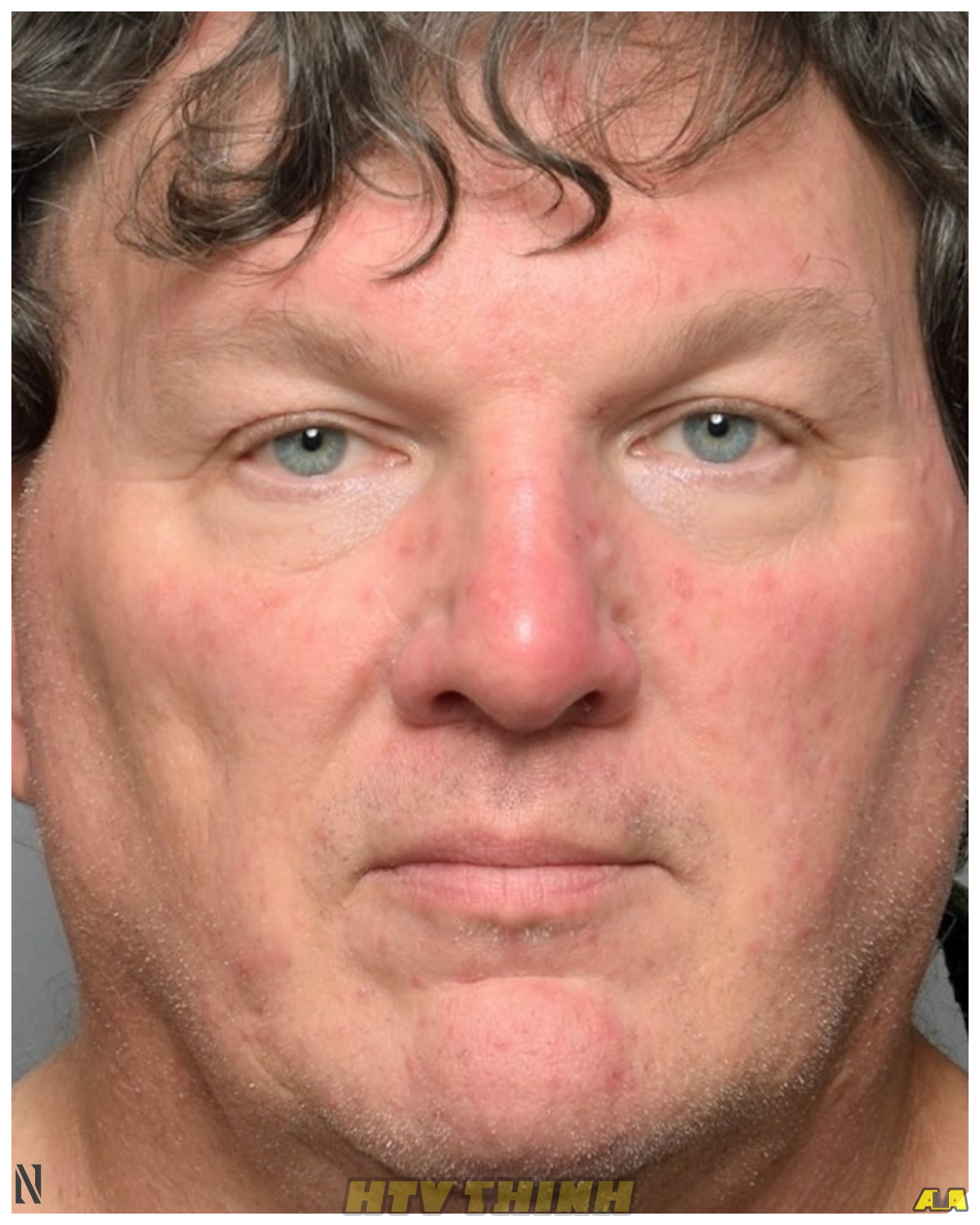
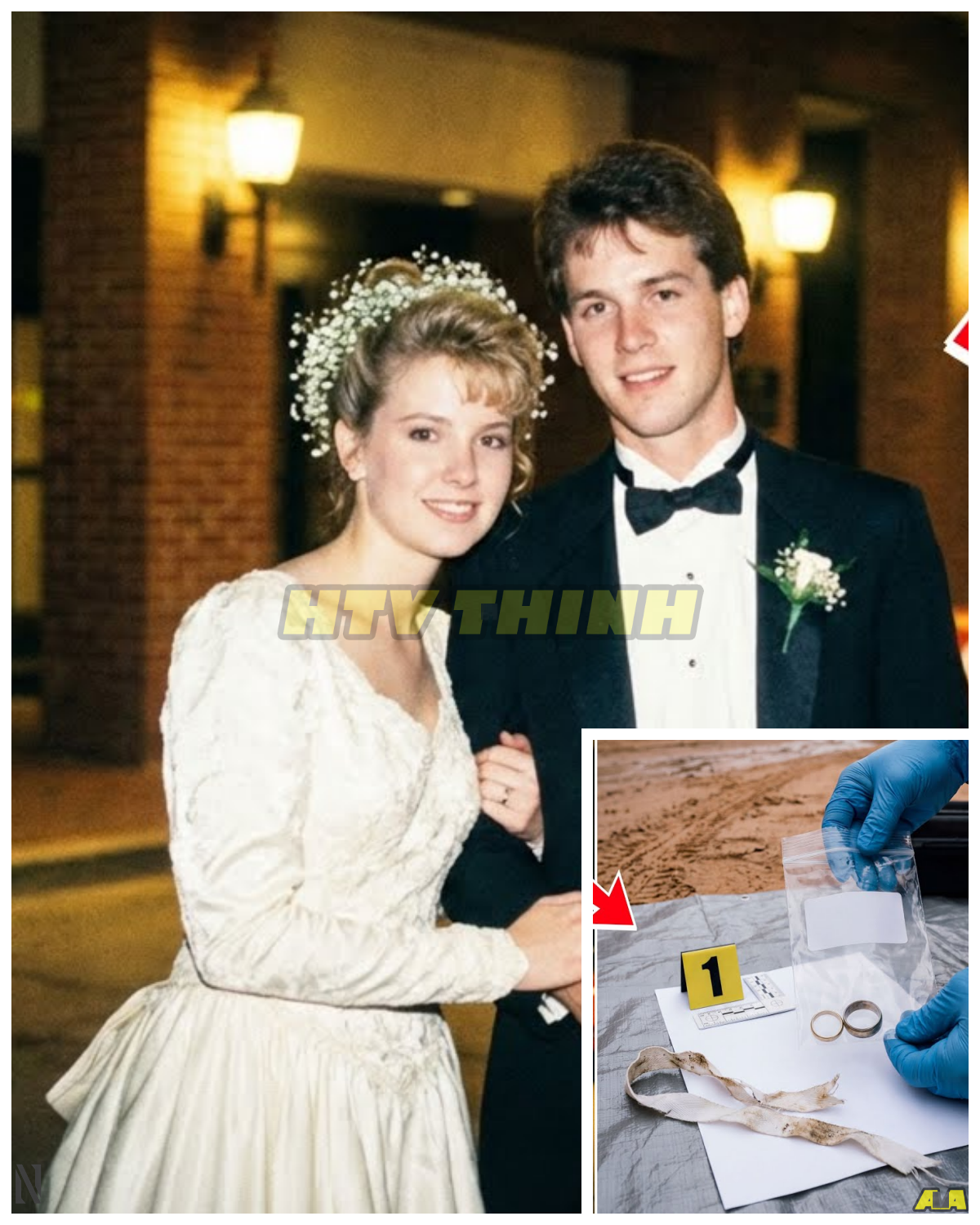
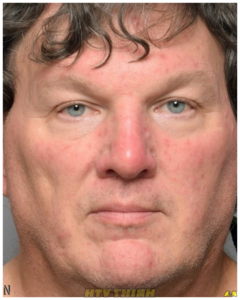
The son-in-law angle.
New perspective.
You have heard the discussion about Tomaso Chion.
You know he was the last known person to see Nancy alive.
You know he drove her home that night.
You know, the sheriff addressed public interest in him by saying he understands why people are looking at the son-in-law.
You have heard the speculation.
You have probably seen the YouTube videos and the Reddit threads and the social media posts.
But I want to approach this from a different angle than most coverage is taken.
Not speculation about guilt or innocence because that is not something we can determine and it is not something we should be declaring without evidence.
Instead, I want to think about this from the perspective of an investigator.
What would a thorough investigator want to know about the last person to see the victim, regardless of who that person was? If you are running this investigation, the first thing you want to know is whether the timeline holds up.
Tomaso reportedly dropped Nancy off at 9:50.
The garage closed, and he drove away.
That is the account.
Law enforcement would want to verify that account against any available evidence.
Phone records, GPS data from his vehicle, traffic camera footage along his route home, surveillance from the neighborhood that might confirm or contradict the departure time.
Any of these data points that cannot be corroborated is a potential problem.
Any that are fully corroborated provides reassurance.
The second thing an investigator would want to know is whether Toamaso had any knowledge of the ransom operation.
Not whether he participated in any way, but whether he might have inadvertently disclosed information to someone, perhaps in conversation or through observable details about his mother-in-law’s routine that a person planning an abduction could have used.
This is not an accusation.
This is standard investigative procedure.
Investigators look at everyone in the victim’s close circle, not because they are all suspects, but because the more you understand about a victim’s world, the more you can narrow down who had access to the specific information the crime required.
The third thing an investigator would want to examine carefully is the ransom note detail about what Nancy was wearing.
If that detail comes from the evening, specifically from the drop off, and Toamasa was there for the drop off, then the person who wrote that note either saw the drop off from outside or obtained that information secondhand from someone who did.
Investigating backwards from that detail is one logical investigative approach.
Sheriff Nanos publicly acknowledged the interest in Tomaso and notably changed the phrasing in official communications from specifically naming Toamaso as the person who drove Nancy home to the more generic family drove her home.
The sheriff said this was to divert speculation from Tomaso.
That is a charitable interpretation.
A less charitable interpretation is that it was an attempt to manage public perception of an ongoing investigative interest.
I am not saying which is true.
I am noting that both interpretations exist.
What I will say is this.
The Guthrie family has publicly stated that they were considering legal action against media personalities who named Tomaso as a suspect without evidence.
That protective stance from the family toward Tomaso is notable and speaks to the family’s confidence in his innocence.
And in the absence of any law enforcement action against him, that family confidence carries real weight.
But the questions around the timeline of January 31st into February 1st remain publicly unanswered.
And until there is an arrest, an explanation, or some form of resolution, those questions will continue to exist.
The border theory, 60 miles in a whole other country.
One of the most significant early investigative developments in this case was the search operation that took place in Rio Rico, Arizona on February 10th.
Rio Rico sits approximately 60 mi south of Tucson.
It sits approximately 10 mi north of the US Mexico border crossing at Ngalas.
Law enforcement detained a person of interest in Rio Rico, searched a vehicle and a property, and released the individual without charges after determining they were not involved.
But the location of that search is worth sitting with for a moment.
The FBI and the Pima County Sheriff’s Department went 60 mi south to the border on the same day they released the doorbell camera footage to the public.
The timing and the location are not accidental.
Law enforcement has never publicly stated that they believe Nancy may have been taken into Mexico.
They have not confirmed or denied this theory.
But the proximity of that Rio Rico operation to the international border is a geographic signal.
Investigators do not conduct major operations 60 mi from the crime scene at random.
They follow evidence.
Something in the investigation led them south.
Something pointed toward the border corridor.
The US Mexico border in the Ngalas area is one of the most complex border crossing zones in North America.
It is a region with deep infrastructure for both legal and illegal crossber movement.
If a person or persons wanted to move a captive elderly woman from Tucson into Mexico within a few hours of an abduction, the Ngalas crossing is the most logical geographic option.
From NY’s home in the Catalina foothills to the Ngalas border, you are looking at roughly an hour and a half to two hours of driving, depending on route.
That timeline is entirely consistent with a departure from Tucson around 2:30 in the morning and an arrival at the border region before sunrise.
If Nancy was taken across the border into Mexico, the investigative picture changes dramatically.
US federal law enforcement, including the FBI, has the ability to cooperate with Mexican authorities through formal channels, but those channels are slower, more bureaucratic, and subject to political complexities that domestic US investigations are not.
The coordination between US and Mexican federal authorities in a kidnapping case can be effective, but it requires time, diplomatic navigation, and the willingness of local Mexican authorities to engage fully.
None of those things are guaranteed.
There is also the cryptocurrency dimension.
Bitcoin was demanded as payment.
Bitcoin does not respect international borders.
A ransom paid in Bitcoin can be instantly received anywhere in the world and moved through multiple wallets in minutes to obscure its origin and destination.
If the ransom operation was designed from the start to have an international component, choosing Bitcoin as the payment method makes complete sense.
It removes the need for any physical transfer of currency.
It bypasses every international financial regulation.
It is in theory completely stateless.
I want to be clear.
We do not know that Nancy is in Mexico.
We have no confirmed evidence of that.
But the pattern of investigative activity in this case, specifically the early focus on the real RICO area and the cryptocurrency demand is consistent with an operation that had an international component built in from the start.
The inside knowledge problem going deeper.
I have touched on this before, but I want to go much deeper on what I am calling the inside knowledge problem because it is the thread that if pulled hard enough may unravel this entire mystery.
Consider everything that whoever took Nancy Guthrie needed to know in order to execute this operation.
First, they needed to know where Nancy lived.
Specifically, not just that Savannah Guthri’s mother lives in Tucson, but the exact address in the Catalina foothills.
That information is not publicly available.
Nancy is not a public figure.
Her address is not listed anywhere obvious.
Second, they needed to know that Nancy would be alone that night.
They needed to know she would be coming home from a dinner at Annie and Tomaso’s house.
That Tomaso would drop her off and that she would be alone in the house from roughly 10:00 in the evening onward.
That is schedule knowledge.
Realtime schedule knowledge, not just general knowledge that Nancy lives alone, but specific knowledge about where she was that Saturday evening and when she would return.
Third, they needed to know about the doorbell camera.
They knew it was there.
They knew enough about it to prepare a method for neutralizing it.
They knew it was a Google Nest device, or at least they knew there was a camera at that specific location on the porch that needed to be dealt with.
Fourth, they apparently knew specific details about what Nancy was wearing that evening.
Details that appeared in the ransom note.
Whether that knowledge came from direct observation of the drop off or from a secondary source, it means someone had eyes on Nancy on the evening of January 31st specifically.
Now, how does someone acquire all of this knowledge? There are really only two credible pathways.
The first is extended professional surveillance conducted over a period of days or weeks prior to the abduction.
following Nancy, learning her schedule, mapping her home, documenting her routines.
This would require significant time investment and would carry real risk of being noticed in a neighborhood where people know each other.
It is possible, but it is a significant undertaking for any criminal operation.
The second pathway is that someone in NY’s life, someone who already had some or all of this information as a natural result of their relationship with her or her family, provided it either knowingly or unknowingly to the people who planned this operation.
This is the inside knowledge theory.
And I want to be extremely careful here because saying this out loud has real implications for real people who have not been charged with any crime.
But I am going to say it anyway because I think it needs to be said directly.
In kidnapping cases involving elderly victims from wealthy or prominent families, the statistical reality is that the vast majority of such cases involve some degree of inside information.
Not necessarily inside participation in the crime itself, but inside information that enabled the crime.
Someone talking to the wrong person.
Someone sharing routine details of a family member’s life in a casual conversation that was overheard or deliberately extracted by a bad actor.
Someone with access to the family’s movements and schedules who was compromised, pressured, or recruited.
Law enforcement knows this.
They knew it from day one.
Every person in Nancy Guthri’s life who had access to her schedule, her address, her routines, and her security setup has been examined as a potential source of inside information.
That examination is ongoing.
It is one of the most sensitive parts of any investigation like this because it requires looking closely at people who may be entirely innocent and deeply grieving and it risks fracturing families and relationships while the investigation continues.
The inside knowledge problem does not point to any specific person, but it is the problem that this investigation has to solve in order to get to the truth.
Because once you identify how the operational information about Nancy got to whoever planned this, you are much closer to identifying who planned it.
The inconsistencies 4 months in, what does not fit? We are now more than 2 months into this investigation and when you lay out everything that is known against everything that does not add up, there are specific inconsistencies that deserve to be named explicitly.
The first inconsistency is the crime scene description.
This has been discussed publicly, but never fully resolved.
Investigators and media reports have offered two fundamentally different descriptions of the interior of NY’s home.
One set of reports described the interior as immaculate.
No signs of a struggle, no ransacked rooms, no overturned furniture.
Another set of reports, including early statements from some family members, described items scattered around and a ransacked appearance.
These are not small differences of interpretation.
They are categorical contradictions.
If the interior of the home was immaculate with the only clear evidence of violence being blood near the front door, then the question becomes how an 84year-old woman with limited mobility was removed from her bed and brought to the front door without any sign of struggle through the living areas of the house.
Either she walked, she was carried, or she was moved in a way that did not leave visible physical evidence of resistance.
Each of those possibilities has different implications.
The second inconsistency is the terrain escape theory.
The official early narrative implied that whoever took Nancy may have exited through the rugged terrain behind the Catalina Foothills property.
Former law enforcement professionals who publicly analyzed this case found this deeply implausible.
Guiding or carrying an elderly woman with limited mobility through rocky Arizona desert terrain in the dark in the early hours of February is not a realistic proposition for a quiet, efficient criminal operation.
If the back terrain escape route is implausible, then there was likely a vehicle.
And if there was a vehicle, there are streets and cameras.
So, where is that footage? The third inconsistency is the glove evidence.
Investigators found a pair of gloves near NY’s home that appeared to match the gloves worn by the suspect in the doorbell camera footage.
The DNA results from those gloves came back and pointed to a local restaurant worker who was determined to have no connection to the case.
Either this is an extraordinary coincidence, a restaurant worker in the same neighborhood happened to discard gloves that looked very similar to the suspect’s gloves at roughly the same time or there is something about how those gloves ended up in that location that still needs explaining.
The restaurant worker explanation was accepted and the lead was closed, but many observers found that result puzzling.
The fourth inconsistency is the supervisor experience issue.
Reporting in early April 2026 raised serious questions about whether the homicide supervisor assigned to oversee this investigation had prior homicide investigative experience.
If it is accurate that the lead supervisor on the most complex and high-profile missing person’s case in Arizona’s recent history had no prior homicide experience.
That is a critical institutional failure.
Homicide investigation requires specific training and experience in evidence collection, crime scene management, and investigative strategy.
A supervisor without that background may have made decisions in the early days of this investigation that compromised evidence or missed opportunities that cannot be recovered.
This is the kind of issue that in a criminal trial becomes a defense attorney’s best argument for case dismissal.
It is deeply concerning.
The fifth inconsistency is the silence on the ransom note verification.
Two ransom notes went to media organizations.
A California man was arrested for sending a fake ransom note.
At no point has law enforcement publicly confirmed that any of the notes to CBS or TMZ were verified as authentic communication from whoever actually took Nancy.
They said they were aware of the notes.
They said they were forwarding materials to investigators, but did they ever confirm that the notes to the media came from the actual abductors? Without that confirmation, we genuinely do not know if the $6 million Bitcoin demand was real or if it was a very elaborate and well-informed fraud.
The public tip problem.
18,000 calls and nothing.
The Guthrie family, the Puma County Sheriff’s Department, and the FBI have received more than 18,000 tips related to NY’s disappearance.
18,000.
That is a staggering volume of information that investigators have had to sort through, verify, and prioritize.
Let us think about what 18,000 tips actually means operationally for an investigation.
Each tip has to be logged, assigned, evaluated, and followed up on.
Even if only 1% of those tips contain potentially actionable information, that is 180 leads that need to be investigated.
At even modest investigative labor requirements per lead, you are talking about thousands of hours of follow-up work.
The volume itself becomes an investigative burden.
And that burden is compounded by the reality of what high volume tip lines look like in high-profile cases.
The vast majority of tips in cases like this come from people with genuine desire to help, but no relevant information.
They saw someone who looked like the suspect description.
They have a neighbor who seemed strange around that time.
They had a dream about it.
They think they know who did it based on a theory they read online.
These are all received, logged, and evaluated.
but they consume investigative resources that might be better deployed elsewhere.
A small number of tips are from people with actual relevant information.
A smaller number still contain information that is genuinely new and not already known to investigators.
And a vanishingly small number of those contain information that is specific and verifiable enough to actually advance the investigation.
In a case with 18,000 tips, that means investigators are essentially looking for a needle in a hay stack made of paper.
There is also the scam dimension that has been widely reported.
Law enforcement issued public warnings about individuals attempting to exploit the Guthrie case to extract money from concerned members of the public.
The California man arrested for sending a fake ransom note to the family was the most visible example of this, but he was unlikely to be the only one.
When a case generates this much national attention, predatory individuals see opportunity.
They see a wealthy, desperate family.
They see an emotionally charged public and they run scams.
Each of those scams represents additional noise in the investigation’s information environment.
The reward structure is worth examining in this context as well.
The $1 million reward announced by the family on February 24th was a genuine attempt to cut through the noise and incentivize people with real information to come forward.
But rewards also generate a specific type of problematic tip.
People who fabricate or embellish information in hopes of qualifying for the payout.
Law enforcement is experienced at handling reward motivated tips with appropriate skepticism, but they still require time and resources to evaluate.
18,000 tips, no confirmed breakthrough.
That is the reality of where this investigation stands.
A moment of honesty.
What this case may be telling us.
I have covered crime for a long time.
Our whole channel is built around understanding cases like this one with depth and honesty.
And I want to take a moment to be completely honest with you about what I see when I look at this case from a high level after 2 months and 16 videos and everything we know.
This case has three possible current states.
Nancy is alive and being held somewhere.
Nancy crossed into Mexico and may or may not be alive.
Nancy did not survive the events of February 1st.
I am not going to pretend those possibilities do not all exist because you already know they do and you deserve honesty from this channel over false comfort.
If Nancy is alive and being held somewhere inside the United States, then the investigative approach of signal sniffers, massive tip volume, and surveillance review should have produced something by now.
The near total absence of confirmed physical evidence of her presence anywhere after February 1st makes domestic captivity an increasingly difficult scenario to explain at this point in the timeline.
If Nancy was taken across the border, the investigation becomes orders of magnitude more complex.
US Mexico law enforcement cooperation in kidnapping cases has a mixed historical record.
If Nancy is being held in Mexico, finding her alive requires diplomatic work and on the ground intelligence that is very different from the domestic investigative tools being used.
And 2 months is a long time for an elderly woman dependent on daily medication to be held in conditions we can only imagine.
The third possibility is the one that the family has acknowledged peripherally and that investigators think about every day.
The pacemaker signal that has not been found.
The medication that was left behind.
The 41 minutes that have not been explained.
The blood near the front door.
The investigation that as of April 2026 has no direct suspect despite the full force of the FBI.
I am not going to state a conclusion here because I genuinely do not know and neither does anyone outside of the investigation.
But what I will say is this.
Hope is not the same thing as evidence.
And an investigation that has been running for 2 months with no arrest, no confirmed proof of life, and no direct suspect is an investigation that is facing very serious obstacles.
That is not a criticism of law enforcement’s effort.
It is an acknowledgment of the reality of what the evidence or the absence of it is communicating.
the technology battle.
How modern criminals think.
I want to spend a little time on something that I think will become increasingly relevant in American criminal cases over the next decade and that this case illustrates clearly.
The deliberate use of technology and technology avoidance in modern criminal operations.
Whoever planned the abduction of Nancy Guthrie made specific choices about technology.
They wore gloves to avoid fingerprints and DNA.
They masked their face.
They used an untraceable generic backpack.
They demanded payment in cryptocurrency.
They communicated through media organizations rather than through traceable direct contact.
They targeted the camera to reduce video evidence.
These are all deliberate technology decisions.
At the same time, they made technological mistakes.
The cloud backup on the Google Nest camera was a critical oversight.
Any person planning a camera disable in 2026 who does not first cut the internet connection to the house is not as technologically sophisticated as they think they are.
The cloud backup runs continuously silently in the background uploading compressed video fragments to Google servers.
Physically tampering with a camera device does not stop the upload.
Only killing the internet connection stops the upload.
Not doing that first was a mistake.
The cryptocurrency demand is interesting in its own right.
Bitcoin is often described as anonymous, but it is not truly anonymous.
It is pseudonmous.
Every Bitcoin transaction is recorded permanently on the public blockchain.
When you pay a Bitcoin address, that transaction is visible to anyone who looks.
The recipient can then move the Bitcoin through multiple wallets to obscure the trail, but each move also leaves a record.
Blockchain forensics has become a sophisticated investigative discipline.
Law enforcement agencies, including the FBI, have entire units dedicated to tracing cryptocurrency transactions.
If a payment was made to the ransom wallet or if the ransom wallet was used in any other transactions, investigators may be able to follow that money through the blockchain.
The FBI has said nothing publicly about whether they have traced any cryptocurrency activity in this case.
But the very fact that they have not announced any results from blockchain analysis does not mean no analysis has been done.
It means they are either still working it or they found something they are not yet ready to disclose.
The signal sniffer deployment is itself a fascinating piece of technology.
Modern law enforcement Bluetooth detection equipment can identify and track low power Bluetooth signals at ranges significantly greater than consumer devices.
The hope that NY’s pacemaker could effectively tell them where she was represents a genuinely new frontier in missing person investigation.
In a world where an increasing number of elderly and medically at risk people carry implanted devices, the potential for those devices to serve as locating beacons in emergency situations is real.
This case has prompted a broader conversation among cardiologists and medical device manufacturers about whether pacemakers and implanted defibrillators should have enhanced emergency tracking features built in.
That conversation is one of the few productive outcomes of this tragedy.
Six things you should watch for as this investigation continues.
There are six specific developments that if any of them happen could break this case wide open.
I want to tell you exactly what to watch for so that when something changes, you understand why it matters.
Watch for news about cryptocurrency wallet activity.
If the FBI makes any announcement that connects a Bitcoin wallet address to a named person or entity, that is a major breakthrough.
| Continue reading…. | ||
| Next » | ||
News
BREAKING: Nancy Guthrie’s 41-Minute Gap Is Finally Explained — Nobody Saw This Chilling Details! – Part 2
Cryptocurrency tracing, when successful, can be devastatingly precise. A single blockchain transaction link can unravel an entire operation. Watch for an announcement about pacemaker signal detection. If law enforcement ever announces that they have detected NY’s pacemaker signal or alternatively that they have confirmed the device is no longer transmitting, either announcement is significant. Detection […]
Nancy Guthrie search: Back door importance, cold case possibility
Let’s bring in Raymond Carr, former FBI special agent and director of the Criminal Justice Institute at Wilmington University. Uh Rey, given what we know at this point and what we just saw in Brian’s piece, how do you think they took Nancy out? It looks like going out the back you go into that […]
FBI Busts $50 Million Hospice Fraud in California — 15 Doctors and Nurses Charged
This morning we executed operation never say die. Federal agents from multiple agencies descended on fraudsters throughout. We’re going to review every single hospice in California to make sure that they’re all appropriate and we hope to do that expeditiously. We’ll do it this year. A federal task force spans out across Southern California and […]
Ukraine has arrived in the Middle East—and the implications could reshape the global balance of power.
Nobody expected Ukraine to show up here. A country fighting for its own survival thousands of miles from the Persian Gulf with no navy to speak of and a war raging on its own soil. And yet, right now, Ukrainian drone experts are on the ground in Saudi Arabia, the UAE, and Qatar. Ukrainian naval […]
Horrifying! Iran fired 450 artillery shells and 25 heat-seeking missiles at US military bases.
Thermonuclear weapons, often referred to as hydrogen based weapons, are governed by strict international frameworks and deterrence strategies. Their use is considered an extreme measure with consequences that extend beyond immediate military objectives. The concept of mutually assured destruction has long shaped global nuclear policy, discouraging any nation from initiating such an attack due to […]
GHOST MURMUER: SECRET CIA Device That TRACKED US F-15 Pilot 40 MILES Away In Iran Through HEARTBEAT!
A man was hiding in silence inside enemy territory and yet his heartbeat gave him away from 40 miles out. This is the story of a secret US operation, a downed fighter jet and a surveillance tool so advanced it can detect the faint rhythm of a human heart across vast distances. It’s called ghost […]
End of content
No more pages to load