A man checks his pager in Beirut.
The screen glows green.
Two words, “Meeting confirmed.
” He clips it back to his belt and walks into the sunlight.
Across the street, a vendor sells oranges.
Children play soccer near a parked car.
Everything appears normal.
A man checks his pager in Beirut.
The screen glows green.
Two words: meeting confirmed.
He clips it back to his belt and walks into the sunlight.
Across the street, a vendor sells oranges.
Children play soccer near a parked car.
Everything appears normal.
What he doesn’t know is that nine months earlier in a warehouse 600 miles away, an intelligence officer photographed that exact device.
Serial number logged, weight measured down to the gram.
A compartment hidden inside, invisible to X-rays, filled with 3 ounces of militaryra explosive.
The pager vibrates again.
He glances down.
Nothing unusual, just another message from his commander.
He has no idea that 12 other men across southern Lebanon just received the same signal.
He has no reason to suspect that the company that manufactured his pager doesn’t exist.
The logo is perfect.
The manual is flawless.
Even the customer service number connects to a real office in Taiwan where operators answer questions about battery life and signal range.
But every call is monitored, every inquiry logged and analyzed.
The operators are real employees working for what they believe is a legitimate electronics company.
They have no idea their entire organization is an intelligence front.
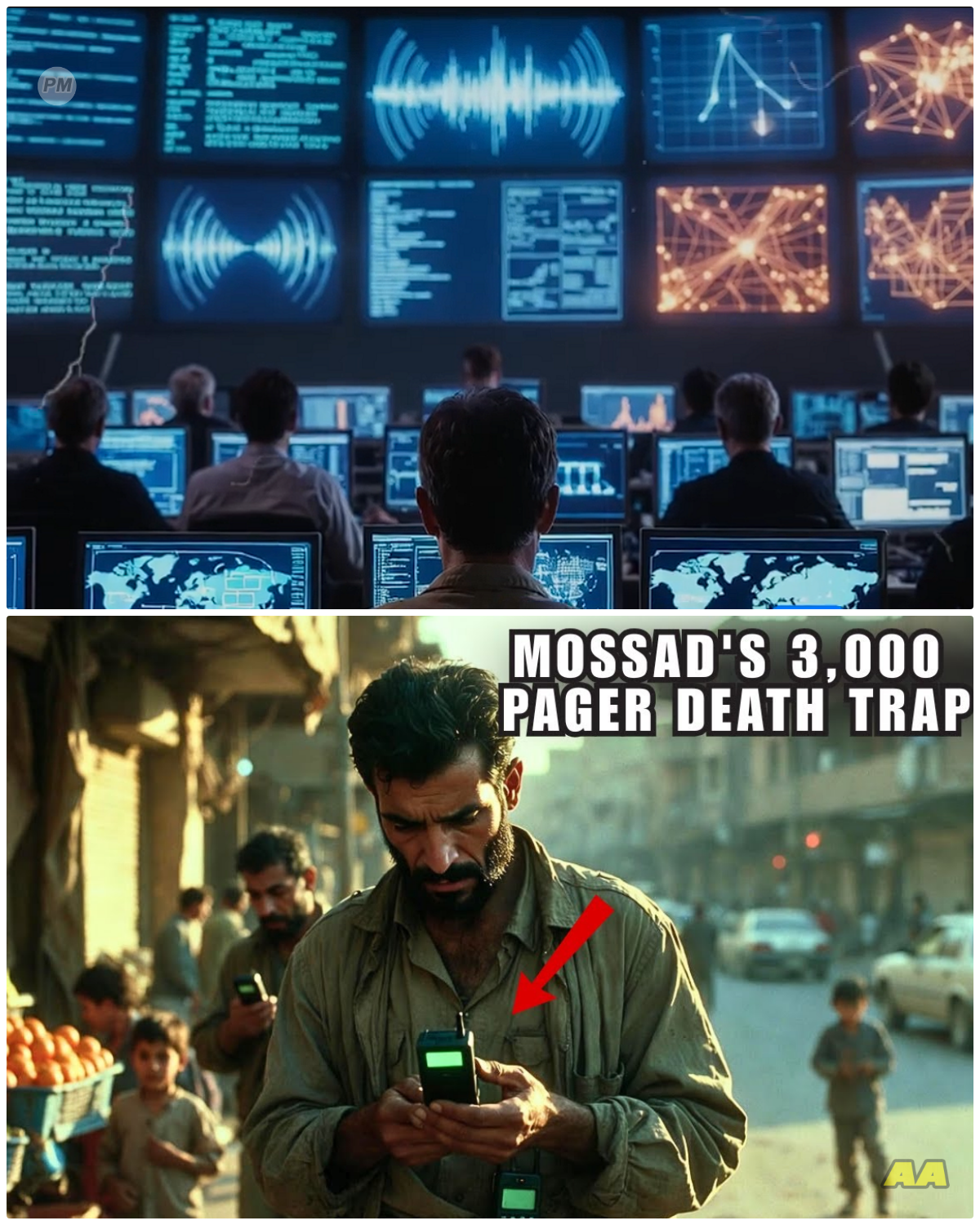
September 17th, 2024, 237 in the afternoon.
3,000 pages detonate simultaneously across Lebanon and Syria.
The operation takes 17 seconds.
Hospitals overflow within minutes.
Hezbollah’s communication network collapses.
Their command structure fragments.
Years of operational security shattered in less time than it takes to read a text message.
This is the story of how intelligence operatives turned everyday technology into precision weapons, infiltrated the most secretive militant organization in the Middle East, and executed an attack so surgically targeted that historians will study it for decades.
But the operation didn’t start in 2024.
It started in a basement office in Tel Aviv 3 years earlier.
The intelligence officer stares at intercepted communications.
Hezbollah has abandoned cell phones.
Too easy to track.
Too vulnerable to hacking.
They’ve switched to pagers.
Old technology harder to trace.
No GPS.
No internet connection.
Just radio frequencies and short numeric codes.
The officer knows this creates a problem.
Pages are anonymous, simple, reliable.
How do you target an enemy when their communication device leaves almost no digital footprint? For months, the intelligence team studies Hezbollah’s communication patterns.
They intercept thousands of pager messages.
Most are coded, brief numeric sequences that mean nothing without context.
But patterns emerge.
Certain numbers appear repeatedly.
Message frequency spikes before operations.
The team begins mapping the network.
Who communicates with whom? Which commanders control which cells? The pager network becomes visible node by node, connection by connection.
The answer comes from an analyst studying supply chains.
Every pager has to come from somewhere.
Every device passes through distributors, wholesalers, shipping companies.
If you can’t hack the device itself, control where it comes from.
The idea is simple, but requires patience.
Create a shell company.
Manufacture pagers.
Make them cheap enough that Hezbollah’s procurement officers can’t resist.
Build trust over years.
Become their preferred supplier.
Then wait.
The proposal reaches senior intelligence officials.
The meeting is tense.
The operation would require massive resources, years of commitment, no guarantee of success.
One official asks the critical question.
What if Hezbollah discovers the modification before activation? The entire operation would be exposed.
assets compromised, future operations endangered.
The risk is substantial, but so is the potential payoff, degrading Hezbollah’s command structure without military invasion, neutralizing thousands of operatives simultaneously, creating operational paralysis that could last months or years.
Authorization is granted with strict conditions.
The shell company must be completely isolated from known intelligence assets, no traceable connections.
If the operation fails, it cannot lead back to Israeli intelligence.
The team begins building a company from scratch.
What Hezbollah’s security teams don’t know is that Israeli intelligence has already mapped their entire procurement network.
They know which front companies Hezbollah uses to purchase electronics.
They know the middlemen who arrange shipments.
They know the warehouses where equipment gets stored before distribution.
Every transaction monitored, every shipment tracked.
The intelligence officers aren’t just watching.
They’re learning the patterns, understanding the trust networks, identifying the gatekeepers who decide which suppliers are reliable and which are suspicious.
A shell company registers in Eastern Europe.
The name sounds generic.
The paperwork is perfect.
The company claims to manufacture affordable communications equipment for businesses in developing markets.
They set up a website, post job openings, hire real employees who have no idea what they’re actually building.
The factory floor operates like any legitimate electronics manufacturer.
Workers assemble circuit boards.
Quality control tests each device.
Shipping departments process orders.
Everything appears legal and routine.
The factory manager is a former electronics engineer with 20 years of industry experience.
He believes he’s been hired to run a startup trying to compete in the budget pager market.
He takes the job seriously, implements quality control protocols, negotiates with component suppliers, attends trade shows to market the products.
He has no idea that four of his employees aren’t really engineers.
They’re intelligence operatives with technical training.
They work second shift.
They have security clearances he doesn’t know exist.
And twice a week they modify a specific percentage of the pages rolling off the production line.
But on a separate floor accessible only through biometric scanners, engineers modify a percentage of the devices.
They create a cavity inside the battery compartment.
The space is minimal, just enough for 3 ounces of PETN plastic explosive, a detonator, and a receiver that responds to a specific radio frequency.
The modification adds 18 g to the device weight.
Testing shows that unless someone dismantles the pager completely and measures each component against factory specifications, the alteration is undetectable.
Even X-ray screening shows nothing unusual.
The explosive is hidden behind shielding that appears identical to standard battery casing.
The technical challenge is substantial.
The explosive must be stable enough to survive shipping and normal use.
The detonator must remain dormant for months, possibly years, without degrading.
The receiver must be sophisticated enough to distinguish the activation signal from normal radio traffic.
Engineers run hundreds of tests.
They drop modified pages from various heights, subject them to extreme temperatures, x-ray them from multiple angles.
The goal is a device that functions normally in every measurable way until the moment of activation.
One engineer proposes adding a timer as a backup detonation mechanism.
The idea is rejected.
If a pager malfunctions and someone tears it apart for repair, a timer would be immediately suspicious.
The explosive must only detonate on command.
No other triggers, no fail safes that could cause premature detonation.
The operation depends on patience and precise coordination.
The first shipment goes to a Lebanese electronics distributor.
50 pages, unmodified, clean devices that perform exactly as advertised.
Hezbollah’s technical teams test them thoroughly.
Battery life exceeds expectations.
Signal range is strong.
The pages are durable, simple to operate, and cost 40% less than competing models.
The distributor places a larger order, 200 units, again, unmodified.
Trust is being built one shipment at a time.
What Hezbollah’s technical team doesn’t realize is that their testing protocols are being observed.
Every test they perform is documented through human intelligence sources.
The Shell company adjusts future modifications based on what Hezbollah checks and what they ignore.
They learn that Hezbollah tests for GPS chips but doesn’t weigh components individually.
They learn that X-ray screening focuses on circuit boards, not battery compartments.
They learn that if a device works reliably for 3 months, subsequent testing becomes routine and superficial.
The intelligence team uses this information to make their modifications even harder to detect.
18 months pass.
The Shell Company has sold over 4,000 pages to various customers across the Middle East.
Most go to legitimate businesses, construction companies, hospitals, security firms.
The devices work perfectly.
No complaints, no defects, no reason for suspicion.
What purchasers don’t know is that intelligence analysts are tracking every sale, identifying which distributors might have connections to Hezbollah’s procurement network.
The company builds a genuine reputation.
Online reviews praise the products.
Industry publications mention them in budget pager roundups.
The website traffic is real.
The customer service is responsive in every measurable way.
This is a functioning business.
Sales representatives travel to trade shows.
Engineers publish technical specifications.
The company pays taxes in three countries.
The cover is so deep that even intelligence agencies in other countries believe it’s legitimate.
A breakthrough comes from financial surveillance.
A specific distributor in Lebanon receives payment from an account linked to a Hezbollah front company.
The transaction is small, routine, buried among hundreds of legitimate purchases.
But the pattern matches intelligence assessments.
This is the entry point.
The next shipment to that distributor contains the modified pagers, 500 units.
Each one carrying its hidden payload.
But there’s a problem.
The modified shipment almost doesn’t happen.
A quality control inspector at the factory notices that a batch of pagers weighs slightly more than specifications indicate.
The difference is minimal, 18 g, but it’s there.
The inspector files a report.
The factory manager schedules a production review for 72 hours.
The entire operation hangs in balance.
If the review goes deep enough, if anyone measures individual components, the modification will be discovered.
The intelligence operatives working undercover at the factory intervene carefully.
They can’t simply override the manager without raising suspicion.
Instead, they provide an explanation.
A batch of higher capacity batteries was installed by mistake.
The weight difference is explained.
The batteries are actually superior, providing longer life.
The manager accepts this.
The review is closed.
The shipment proceeds.
What he doesn’t know is that those operatives spent an entire night recalibrating every modified pager in that batch, ensuring the weight distribution appeared consistent with the battery explanation.
Hezbollah’s
procurement officers inspect the new shipment.
They test random samples, disassemble several units, check for GPS chips, hidden transmitters, any sign of compromise.
They find nothing.
The devices pass every security protocol.
What they can’t detect is that the explosive compound is chemically stable, generates no electromagnetic signature, and the detonator is powered by a capacitor that remains dormant until activated by a specific frequency transmission.
The pages are distributed to mid-level commanders, communications officers, logistics coordinators, exactly the personnel intelligence analysts wanted to target.
A Hezbollah commander receives his pager in March 20.
Sir 24.
He’s cautious.
He survived two decades of Israeli intelligence operations by trusting nothing.
He has the device examined by his personal security team.
They disassemble it completely, check every component, run it through multiple scanners.
They find a well-manufactured pager with no suspicious elements.
He begins using it daily.
Messages from superiors, coordination with subordinates, meeting times, status updates.
The device becomes essential to his operations.
What he can’t see is that every message he receives is being intercepted and analyzed 200 km away.
Intelligence officers are building a complete picture of his network, his schedule, his habits.
They’re not just preparing to eliminate him.
They’re preparing to eliminate his entire command structure simultaneously.
3 months later, another shipment.
800 pagers, then another 1,500.
By September 2024, nearly 3,000 modified devices are in circulation, clipped to belts and sitting on desks across Lebanon and Syria.
Each one is a small patient bomb waiting for a signal that will come from a transmitter station 200 km away.
But the intelligence team faces a growing problem.
The longer the operation continues, the higher the risk of discovery.
Every day, thousands of people use these devices.
Every day brings a chance that someone will notice something unusual.
A pager dropped from a height that cracks the casing.
A techsavvy member who decides to modify his device for better reception.
A bomb sniffing dog at a checkpoint that alerts to explosive residue.
The operation is on a timer and no one knows exactly when it will expire.
Before we continue, here’s a question.
Drop your answer in the comments.
When intelligence agencies turn consumer electronics into weapons, does precision justify the method, or does it cross a line that changes the rules of conflict? The planners face a critical challenge.
Timing.
Detonate too early and the operation’s full potential is wasted.
Wait too long and someone might discover the modification.
One engineer accidentally dropping a pager.
One curious technician deciding to fully disassemble a device.
One X-ray operator noticing an anomaly.
Every day increases the risk of exposure.
Intelligence officers monitor Hezbollah’s communication patterns, looking for the optimal moment when maximum number of targets will be carrying their pagers.
The team analyzes thousands of intercepted messages.
They identify patterns.
Monday mornings see high communication volume as commanders coordinate weekly operations.
Friday afternoons see reduced traffic as members prepare for the weekend.
The ideal window is midafter afternoon on a weekday.
Maximum personnel on duty.
Maximum pagers active and in use.
Minimum civilian presence in operational areas.
But there’s another factor.
Hezbollah has begun discussing procurement of new communication equipment.
Intercepted conversations mention concerns about pager range limitations.
Some members suggest upgrading to more modern devices.
If Hezbollah switches communication systems, the entire operation becomes worthless.
3 years of preparation, millions in resources, all for nothing.
The decision is made.
The operation must proceed within weeks.
September 17th is chosen for a specific reason.
Intelligence intercepts indicate a major communication drill scheduled for that afternoon.
Hezbollah commanders will be testing their pager network, ensuring message relay systems function properly.
Nearly everyone with a modified device will have it on their person, powered on, ready to receive signals.
The window is perfect.
The morning of September 17th, a Hezbollah communications officer in southern Lebanon wakes at 6:15.
He showers, dresses, checks his pager.
One new message, a routine logistics update.
He clips the device to his belt and makes coffee.
His wife asks about dinner plans.
He says he’ll be home by 7.
What he doesn’t know is that 200 km away, intelligence officers are running final systems checks on transmission equipment, frequencies calibrated, encryption codes verified, fail safes tested.
The detonation signal is loaded and ready.
All that remains is authorization from command level.
He kisses his children before they leave for school.
His daughter is excited about a science project.
His son complains about mathematics homework.
Normal morning chaos.
He reminds them to behave, to study hard.
He tells them he loves them.
He has no idea these are the last words he’ll ever speak to his children.
No idea that in 8 hours his wife will receive a phone call that destroys their family.
no idea that the device on his belt, which he’s carried everyday for 6 months, which has never given him any reason for concern, is about to explode.
At 9:30, a meeting convenes in Tel Aviv.
Senior intelligence officials review the operation one final time.
Target distribution maps displayed on screens.
Hospital capacity assessments in Lebanese cities analyzed.
Risk evaluation reports examined.
The discussion is clinical, focused on operational effectiveness versus potential collateral damage.
The modified pages are designed to direct explosive force outward in a tight radius.
Maximum damage to the person carrying the device.
Minimal risk to bystanders more than 2 m away.
But minimal doesn’t mean zero.
One official raises concerns about timing.
If the detonations occur in crowded areas, there will be civilian casualties.
children near members when devices explode.
Bystanders caught in the blast radius.
The operation is surgical, but surgery still causes collateral damage.
The counterargument is immediate compared to air strikes, artillery bombardment, or ground invasion.
The collateral damage will be exponentially lower.
Traditional military operations to achieve the same objective would kill thousands of civilians.
The pager attack will harm dozens at most.
The math is brutal but clear.
Authorization is granted at 10:47.
The communications officer attends a briefing at noon.
23 Hezbollah members in the same room.
16 are carrying modified pagers.
The briefing covers supply route coordination.
Weapon shipment schedules.
Nothing unusual.
The meeting ends at 1:15.
Everyone disperses.
Some drive home.
Others head to secondary locations.
Three go to a market to buy groceries.
They move through crowds past civilians, unaware that they’re carrying active explosive devices that will detonate in 78 minutes.
One of the men stops at a street vendor to buy fruit.
He selects oranges carefully, checking for ripeness.
The vendor jokes about his selectiveness.
They laugh.
The man pays, takes his bag, continues walking.
His pager is clipped to his belt, pressed against his abdomen.
In 74 minutes, the explosive will detonate inward, shredding his internal organs.
He’ll die within minutes.
But right now, he’s thinking about oranges, about whether his wife will be pleased with his selection, about the price he paid.
Normal thoughts, normal concerns.
He has no sense of the violence waiting inside the device on his belt.
At 2:20, a technical team in Israel begins the transmission sequence.
The room is silent.
23 personnel monitoring various systems, communications, medical response in Lebanese hospitals, intelligence intercepts.
Everyone knows what’s about to happen.
Some have worked on this operation for 3 years.
Others joined recently, briefed only on their specific role.
All understand the magnitude.
This is unprecedented.
No intelligence operation in history has simultaneous targeted this many individuals across such a wide geographic area.
The signal is disguised as a routine system message.
To anyone monitoring radio frequencies, it appears identical to standard pager traffic.
Numeric codes, brief, unremarkable.
But embedded in the transmission is a specific frequency pattern that activates the dormant detonators.
The signal travels at the speed of light, bouncing off relay stations, spreading across Lebanon and Syria, reaching every modified pager simultaneously.
The transmission takes 11 seconds.
Then comes the waiting.
Radio waves travel fast, but detonation sequences have built-in delays.
Micros secondsonds for capacitors to charge.
Micros seconds for detonators to reach critical temperature.
The technical team counts down.
5 seconds.
4 3 2 1 2 37 in the afternoon.
A man in Beirut feels his pager vibrate.
He reaches for it.
The screen shows a message.
He leans closer to read.
The device explodes in his hand.
The force rips through flesh and bone.
His fingers disappear.
The blast tears into his face and chest.
He collapses.
Blood pooling.
People around him scream.
Some run.
Others freeze, unable to process what just happened.
17 seconds.
That’s how long it takes for 3,000 devices to detonate across two countries.
A commander in southern Lebanon is driving when his pager explodes.
The car swerves off the road.
A logistics officer is standing in a grocery store.
The blast throws him backward into a shelf.
Products scatter.
A communication specialist is sitting in a cafe.
The explosion draws every eye in the room.
Smoke, confusion, blood spreading across the floor.
A father is picking up his daughter from school.
He’s early.
He waits outside, checking his pager for messages.
The device explodes while he’s holding it near his face.
His daughter, 10 ft away, sees everything.
The flash, the blood, her father falling.
She screams.
Other parents rush over.
Someone calls for help.
The daughter is physically unharmed but will carry the psychological trauma of her life.
She saw her father’s face destroyed in an instant.
Saw him collapse.
Saw the blood spreading across the pavement.
What she doesn’t understand, what she can’t understand is that this was planned.
That someone somewhere decided her father needed to die.
That they spent years preparing his death.
That they turned a communication device into a weapon specifically to kill him and thousands like him.
What none of them knew was that they were part of the largest simultaneous targeted attack in modern intelligence history.
Hospitals are overwhelmed within minutes.
Emergency rooms flood with casualties.
Doctors see injuries they’ve never encountered.
Hands shredded, faces destroyed.
Abdominal wounds from devices clipped to belts.
The injuries are distinctive, localized, precise.
Medical staff realized quickly this wasn’t random.
These are coordinated detonations.
Someone turned communication devices into weapons.
A surgeon at a Beirut hospital performs emergency surgery on a patient with catastrophic hand injuries.
Both hands are gone.
The face is severely damaged.
The abdomen shows blast trauma.
As she works, another casualty arrives with identical injuries.
Then another, then five more.
The pattern is unmistakable.
All male, all similar age, all carrying pagers.
The surgeon understands immediately this is a coordinated attack, but the scale is overwhelming.
Her hospital has 50 casualties.
Reports from other facilities indicate hundreds more.
How do you coordinate an attack this large without anyone noticing? The surgeon works for 18 hours straight.
She saves some patients, loses others.
The ones who survive face permanent disabilities, blindness, lost limbs, cognitive damage from blast trauma.
These aren’t injuries that heal.
These are life sentences.
Families destroyed, careers ended, independence lost, all in 17 seconds.
Hezbollah’s command structure fractures immediately.
Communications officers are dead or incapacitated.
The pager network they relied on is gone.
Commanders can’t reach subordinates.
Units are isolated.
The organization’s operational security built over decades collapses in 17 seconds.
They’re forced back onto cell.
Phones, which they know are compromised.
Every call monitored, every message intercepted.
The intelligence advantage shifts completely.
Within 2 hours, Hezbollah’s leadership realizes the scale of the operation.
This wasn’t an air strike.
No missiles, no drones, no warning.
Just devices they trusted turned against them.
The paranoia spreads fast.
If the pagers were compromised, what else is? Radios, laptops, vehicles.
Every piece of equipment becomes suspect.
Operational paralysis sets in.
A senior commander convenes an emergency meeting.
He uses a cell phone despite knowing it’s monitored.
He has no choice.
The pager network is gone.
He needs to coordinate response, assess damage, restore some semblance of command structure.
The call is intercepted immediately.
Intelligence analysts listen in real time.
They hear confusion, anger, disbelief.
The commander is asking questions no one can answer.
How did this happen? Who approved the pager purchase? Which supplier provided them? The questions reveal the operation’s success.
Hezbollah has no idea how deeply they were penetrated.
Intelligence analysts monitor the aftermath in real time.
Intercepted communications show confusion, anger, disbelief.
Hezbollah members are asking how this happened.
Who approved the pager purchase? Which supplier provided them? How did no one detect the modification? The questions have no good answers.
The supply chain was clean.
The devices worked perfectly for months.
Every security protocol was followed.
Yet somehow, Israeli intelligence had turned their communication lifeline into a mass casualty weapon.
The technical investigation begins immediately.
Hezbollah collects fragments from detonated pagers, bomb specialists examine the remains.
What they find is sophisticated beyond their expectations, militaryra explosive, professional detonator design, miniaturized receiver circuits.
This wasn’t improvised.
This was precision engineering.
The specialists estimate the modification required clean room facilities, specialized tools, and extensive testing.
This was a state level operation, not something a small cell could accomplish.
The realization is chilling.
If a state intelligence agency could compromise their pagers, they could compromise anything.
But the operation wasn’t just about casualties.
It was about psychology.
Hezbollah prided itself on operational security.
They believed their networks were impenetrable.
They thought switching to low tech devices made them safer.
The pager attack shattered that confidence.
If intelligence agencies could compromise something as simple as a pager, they could compromise anything.
The fear becomes paralyzing.
Trust evaporates.
Members start suspecting each other.
Was someone on the inside helping? Did someone inform the Israelis about their supply chain? Internal investigations turn aggressive.
Anyone involved in pager procurement is questioned.
Suppliers are audited.
Middle men interrogated.
The search for blame becomes destructive.
Members who had nothing to do with procurement fall under suspicion simply because they asked fewer questions.
The paranoia erodess organizational cohesion.
People who trusted each other for years suddenly wonder if their colleague is an intelligence asset.
The psychological damage exceeds the physical casualties.
The international reaction is swift and divided.
Some countries condemn the attack as indiscriminate terrorism.
Others view it as precision targeting of military personnel.
Legal experts debate whether turning consumer electronics into weapons violates international law.
The arguments are complex.
The devices only harmed individuals carrying them.
The targets were members of a designated militant organization.
But the method was unprecedented.
No warning, no ability to surrender, just instant detonation.
United Nations debates are heated.
Representatives from Lebanon present images of casualties, civilian bystanders injured in blasts, children traumatized by witnessing explosions.
They argue the attack violates principles of distinction and proportionality.
How can you ensure civilians aren’t harmed when the weapon is a common communication device? What if a member handed his pager to a child seconds before detonation? What if a civilian picked up a dropped pager? Intelligence officials defend the operation on tactical grounds.
3,000 Hezbollah operatives neutralized without air strikes, without ground invasion, without significant civilian casualties.
The precision was surgical, the impact devastating.
Traditional military operations would have required massive force and caused far more collateral damage.
The pager attack achieved strategic objectives with minimal infrastructure destruction, no buildings demolished, no neighborhoods leveled, just targeted elimination of militant personnel.
But critics point out the implications.
If one intelligence agency can weaponize pagers, others can weaponize anything.
Phones, laptops, smart watches.
The precedent is terrifying.
Everyday technology becomes potential weapons.
The line between civilian and military infrastructure blurs.
How do you protect yourself when the device in your pocket might explode? How do you maintain trust in technology when any device could be compromised? Technology companies face immediate backlash.
Consumer trust in electronics plummets in certain regions.
People demand proof that their devices haven’t been modified.
But how do you prove a negative? How do you demonstrate that a device is safe when sophisticated modifications are undetectable without complete disassembly? Some companies offer free security inspections.
Others provide detailed manufacturing documentation.
But the uncertainty persists.
The pager attack introduced doubt into the consumer electronic supply chain that will take years to overcome.
The technical details emerge slowly.
Forensic analysts examined fragments.
The explosive was high-grade PETN, stable and difficult to detect.
The detonators were triggered by a specific radio frequency transmission.
The modification was so sophisticated that even experienced bomb technicians are impressed.
This wasn’t crude improvisation.
It was precision engineering executed over years.
The level of technical sophistication suggests state sponsored operations with substantial resources.
Not the work of a small intelligence cell, but a coordinated effort involving dozens of specialists and millions in funding.
Hezbollah launches an internal investigation.
They audit their entire procurement network.
Every supplier scrutinized, every middleman questioned.
They trace the pagers back to the Shell Company in Eastern Europe.
But when investigators arrive, the office is empty.
Lease terminated days before the attack.
Bank accounts closed.
Website offline.
employees vanished.
The company existed long enough to build trust and deliver its payload, then disappeared like it never existed.
The factory manager reads about the pager attack in the news.
He sees images of casualties, reports describing modified pagers with hidden explosives.
Then he sees the company logo, his company, the business he managed for 3 years.
He realizes immediately what happened.
His factory produced those devices.
His employees assembled them under his supervision.
He thinks back to the four engineers who worked second shift, the ones who kept to themselves, who had special access to secure areas, who occasionally worked through the night on what they called quality control testing.
He understands now.
He was part of an intelligence operation.
He managed a weapons factory disguised as an electronics manufacturer.
The realization destroys him.
He quits electronics entirely, changes careers, moves to another country.
But the guilt follows.
He supervised the production of devices that killed thousands.
That he never knew doesn’t matter.
He still feels responsible.
The operation reveals how deeply intelligence agencies can penetrate enemy networks.
The planning required years, multiple layers of cover, coordination across manufacturing, shipping, financial systems, hundreds of people involved, most unaware of the operation’s true purpose.
The compartmentalization was flawless.
No leaks, no warnings, no one suspected until 3,000 devices exploded simultaneously.
6 weeks after the attack, Hezbollah is still struggling to rebuild communication systems.
They’ve abandoned pagers entirely.
Cell phone usage has increased despite knowing it’s monitored.
Encrypted messaging apps are unreliable.
Face-to-face meetings are the only safe option, but those are slow and vulnerable to surveillance.
The organization’s operational tempo has decreased significantly.
Planned operations delayed, coordination fractured.
The pager attack achieved what years of air strikes couldn’t.
It broke their ability to function as a cohesive military force.
But the story doesn’t end with tactical victory.
The operation raises questions about the future of conflict.
If intelligence agencies can turn electronics into weapons, where does it stop? Could they weaponize medical devices, vehicles, home appliances? The technology exists.
The precedent is set.
The question isn’t whether it’s possible.
It’s whether anyone will use it again.
Cyber security experts begin analyzing potential vulnerabilities.
Pacemakers have wireless communication capabilities.
Could they be hacked and weaponized? Vehicle control systems are increasingly computerized.
Could intelligence agencies modify them to cause crashes? Smart home devices connect to the internet.
Could they be turned into surveillance tools or weapons? The pager attack opened a door that many experts wish had remained closed.
It demonstrated that with enough resources and patience, any electronic device can become a weapon.
Some intelligence analysts believe the pager operation was a one-time success that won’t be replicated.
The element of surprise is gone.
Organizations will now scrutinize every device.
Supply chains will be fortified.
The window that made this operation possible has closed.
Others argue that the window never closes.
It just shifts.
As long as organizations rely on technology, vulnerabilities exist.
The next target might not be pagers.
It might be something more common, more trusted, more integrated into daily life.
The human cost is documented but impersonal.
Casualty numbers released, medical reports filed, families mourn.
But behind each statistic is someone who trusted a device, followed security protocols, and died because intelligence operatives spent years preparing to turn that trust into a weapon.
The moral calculus is uncomfortable.
These were enemy combatants, but they were killed by devices they had no reason to suspect.
No chance to fight back.
No moment to realize the threat.
A widow sits in her home 3 months after the attack.
Her husband is gone.
Her children ask when father is coming home.
She doesn’t know how to explain that he’s not that he died when his pager exploded.
They don’t understand what a pager is.
Don’t understand how a communication device can kill someone.
She barely understands it herself.
The explanation she received from officials was technical, detailed, incomprehensible.
All she knows is that her husband went to work and never came home.
That something he carried every day.
Something he trusted killed him.
The randomness feels cruel.
If he had left the pager at home that day.
If he had been in a different location, if the attack had come an hour earlier or later, small changes that would have meant life instead of death.
The operation succeeds because it exploits the fundamental human need to communicate.
Organizations can’t function in isolation.
Commands must be relayed, plans coordinated, intelligence shared.
Hezbollah tried to secure that communication by using simple analog technology.
They believed low tech meant low risk.
They were wrong.
The vulnerability wasn’t in the technologies complexity.
It was in the supply chain, in the trust placed in manufacturers and distributors, in the assumption that if a device worked properly for months, it must be safe.
Israeli intelligence understood this.
They didn’t need to hack sophisticated systems.
They needed patience.
They needed to build trust over years.
They needed to think like their enemy, understand what they valued, and turn that into a weakness.
The pager operation was less about technology and more about psychology, about understanding how organizations make decisions, how they assess risk, how they build trust, and how that trust can be weaponized.
The aftermath reveals something deeper about modern intelligence work.
Operations aren’t executed in days or weeks.
They unfold over years.
Assets positioned, cover stories built, supply chains infiltrated, every step carefully planned, every contingency considered.
The pager attack looked like 17 seconds of violence.
But it was 3 years of preparation.
3 years of intelligence officers running a fake company, manufacturing real products, building legitimate business relationships, all to deliver a payload that would be activated in a single coordinated moment.
Hezbollah’s counter intelligence teams now face an impossible task.
How do you secure an organization when any device might be compromised? How do you rebuild trust when the previous system was penetrated so completely? They can’t abandon technology entirely.
They need communication.
But every new system carries risk.
Every supplier could be another front.
Every device another potential weapon.
The paranoia becomes operational constraint.
They implement new protocols.
All electronics must be purchased from at least three separate suppliers.
Random devices are selected for complete disassembly and analysis.
Weight specifications must match factory documentation exactly.
Suppliers must provide manufacturing facility access for inspection.
But even these measures provide limited security.
If an intelligence agency controls the manufacturer, supplier verification is meaningless.
If the modification is sophisticated enough, disassembly won’t reveal it.
The protocols provide psychological comfort more than actual security.
This is the true impact of the operation.
Not the casualties, not the immediate tactical advantage, but the long-term psychological effect.
Hezbollah now operates in constant suspicion.
Their decision-making is slower, their coordination weaker, their confidence shaken.
Intelligence analysts calculate that the operation’s real value isn’t the 3,000 operatives neutralized.
It’s the degradation of organizational effectiveness that persists long after the explosions faded.
The pager attack also sends a message to other organizations.
If Israeli intelligence can do this to Hezbollah, they can do it to anyone.
The operation demonstrates capabilities that most intelligence agencies never reveal.
operational depth, technical, sophistication, patience, the ability to maintain cover for years without exposure.
Other groups take notice, security protocols are revised, trust networks reassessed, but the fundamental problem remains.
Organizations need technology, and technology requires supply chains.
Supply chains can be infiltrated.
There’s no perfect defense.
Some intelligence officials privately acknowledge that the pager operation represents both a triumph and a problem.
The triumph is obvious.
Unprecedented precision, devastating impact, perfect execution.
But the problem is precedent.
Other agencies will study this operation.
They’ll adapt the method.
They’ll look for ways to replicate the success.
The weaponization of consumer electronics could become normalized.
What was once unthinkable becomes standard practice.
Chinese intelligence analysts study the operation extensively.
They see applications beyond military targets.
Political dissident, protest organizers, journalists, anyone who poses a threat to state interests could be targeted through compromised electronics.
The technical barriers are substantial but not insurmountable.
Russian intelligence reaches similar conclusions.
The pager attack demonstrates that conventional warfare is evolving.
The battlefield is everywhere.
Every device is a potential weapon.
Every supply chain a potential infiltration point.
The legal and ethical debates continue.
International law struggles to classify the operation.
It wasn’t a traditional military strike.
It wasn’t terrorism in the conventional sense.
It was something new, a hybrid operation that exploited the gap between warfare and espionage.
The pagers were weapons, but they were also communication devices.
The targets were militants, but they were killed without engagement.
The method was precise, but it relied on deception that lasted years.
Legal scholars proposed new frameworks for evaluating such operations.
They argue that international law written for 20th century warfare doesn’t adequately address 21st century tactics.
The Geneva Conventions discuss proportionality, distinction, necessity.
But how do those principles apply when the weapon is indistinguishable from civilian technology? When the attack happens in peace time, when there’s no declaration of war, no front lines, no uniformed combatants, the debates remain unresolved.
Some countries push for international treaties banning weaponized consumer electronics.
Others argue that such treaties are uninforcable.
How do you verify compliance? How do you inspect every electronics manufacturer globally? How do you distinguish legitimate products from weapons? The technical challenges of enforcement make regulation nearly impossible.
Historians will likely view the September 17th pager attack as a watershed moment.
The day intelligence operations crossed into territory previously reserved for science fiction.
The day everyday technology became undeniably weaponized.
The day organizations realized that their greatest vulnerability wasn’t their military capacity or their operational security, but the trust they placed in objects they used everyday.
For the man who checked his pager in Beirut that morning, none of this matters.
He’s one of the casualties, a statistic in an intelligence report.
His final moments were ordinary.
A message received, a glance at a screen, then nothing.
He never knew about the warehouse where his device was modified.
Never knew about the Shell company that manufactured it.
Never knew about the intelligence officers who spent years planning his death.
He trusted the device because it worked, because it was reliable, because he had no reason to doubt it.
That trust was his vulnerability.
And in the end, it was enough.
The operation proves something fundamental about modern conflict.
Victory doesn’t always come from superior firepower.
Sometimes it comes from patience, from understanding your enemy so completely that you can turn their own tools against them.
From building trust so carefully that suspicion never takes root until it’s too late.
The pager attack wasn’t one in 17 seconds.
It was one in 3 years of preparation.
Three years of operatives maintaining cover.
Three years of a fake company building legitimate credibility.
Three years of intelligence analysts tracking procurement networks and communication patterns, waiting for the perfect moment to activate thousands of hidden weapons simultaneously.
Hezbollah’s leadership now understands they were outplayed at a level they didn’t know was possible.
Their security protocols were thorough.
Their procurement network was careful.
Their operational discipline was strong.
But none of it mattered because Israeli intelligence didn’t attack their systems.
They became part of their systems.
They didn’t breach security.
They were the supplier.
They didn’t hack communication devices.
They built them.
The intelligence officers who executed this operation demonstrated something that will influence tactics for decades.
They showed that the most effective attacks aren’t necessarily the most violent.
They’re the most patient.
The ones that exploit trust rather than overwhelming force.
The ones that turn an enemy’s strength into weakness.
Hezbollah’s strength was operational security.
Their careful procurement networks.
Their distrust of modern hackable technology.
Israeli intelligence turned all of that into vulnerability.
They made Hezbollah’s caution work against them.
This is the lesson the pager operation teaches.
In modern intelligence warfare, the greatest threats don’t come from outside.
They come from inside.
From the trusted supplier, the reliable manufacturer, the vetted distributor, from the devices that work exactly as promised month after month until the moment they don’t, until they explode, until 17 seconds of coordinated detonations dismantle an organization’s communication network and shatter the illusion that anything can truly be secured.
The psychological warfare component extends beyond Hezbollah.
Other organizations watching the operation draw immediate conclusions.
If communication devices can be weaponized, what about weapons themselves? If Israeli intelligence can compromise supply chains, could they compromise ammunition? Could a shipment of rifles contain tracking devices? Could artillery shells be modified to malfunction? The questions multiply.
Trust in equipment evaporates.
military organizations begin implementing verification protocols that slow procurement and increase costs.
The pager attacks impact ripples outward, degrading operational effectiveness of groups that weren’t even targeted.
This broader psychological impact was likely calculated.
Intelligence planners understood that the operation would generate fear beyond its immediate victims.
That other organizations would respond by implementing security measures that hamper their own effectiveness.
That the precedent would create uncertainty that persists long after the physical damage healed.
The pager attack was as much about perception as destruction, about demonstrating capabilities that make enemies question everything they trust.
The intelligence officers who plan this operation will never be named.
Their work will remain classified for decades.
But they’ve changed how future conflicts will be fought.
They’ve demonstrated that with enough patience, enough resources, enough understanding of an enemy’s trust networks, everyday technology can become the most effective weapon.
Not because it’s complex, because it’s simple, because it’s trusted.
Because no one suspects the device they’ve used for months could be the thing that kills them.
The operational security required for this attack was extraordinary.
Hundreds of people involved over 3 years, factory workers, sales representatives, customer service agents, shipping coordinators.
Most had no idea what they were part of.
The compartmentalization had to be perfect.
One person asking the wrong questions, one employee noticing suspicious activity, one security audit that went too deep.
Any of these could have compromised the entire operation.
That it succeeded demonstrates intelligence tradecraft at the highest level.
Future operations will be studied against this benchmark.
The pager attack represents what’s possible when intelligence agencies commit fully to long-term strategic operations.
when they prioritize patience over immediate results.
When they accept that the best attacks take years to prepare and seconds to execute.
This approach requires institutional commitment that many agencies lack.
It requires maintaining cover operations for years with no guarantee of success.
It requires resources invested in something that might never activate.
But when it works, the results speak for themselves.
If this exposed the invisible machinery of modern intelligence operations, subscribe for the next story and drop a comment.
| Continue reading…. | ||
| Next » | ||
News
“From Sweet Success to Bitter End: The Shocking Downfall of Cake Boss Buddy Valastro!” Buddy Valastro, the charismatic face of Cake Boss, once ruled the culinary world with his extravagant cakes and larger-than-life personality, but now his empire is crumbling! What led to the dramatic decline of this beloved baking show? Behind the frosting and fondant lies a tale of betrayal, scandal, and secrets that will leave fans reeling. As we dig deep into the rise and fall of Buddy Valastro, you’ll uncover the shocking truths that could change everything you thought you knew about the Cake Boss! 👇
One of the things that I love most about my show is that when I travel the world, a lot of people tell me that we inspire them to want to bake. We inspired them to, you know, want to go to culinary school. In the world of reality television and culinary shows, one name […]
“Melissa Gilbert Reveals Shocking Secrets About Dean Butler: The Truth Behind Their Iconic Romance!” For decades, fans have been captivated by the on-screen chemistry between Melissa Gilbert and Dean Butler, but now the beloved star is breaking her silence with revelations that will leave you gasping! Why did Melissa choose to stay quiet for so long, and what explosive truths has she finally decided to unveil? As she peels back the layers of their storied past, prepare for a rollercoaster of emotions that shatters the illusion of their perfect love story. You won’t believe what she has to say! 👇
Little House in the Prairie is a reminder of when things were simpler for us in our lives those 45 years ago. Why did Melissa Gilbert stay silent all these years about Dean Butler? And why is she finally speaking now? Because of what she just revealed. No one saw it coming. Not her longtime […]
“The Untold Betrayal: How Michael Anthony’s Loyalty to Van Halen Crumbled in the Shadows of Fame!” Michael Anthony, the man behind the legendary riffs of Van Halen, has silently endured shocking betrayals that no one could have imagined, as his loyalty was brutally tested. From dark secrets to fractured relationships, his story is not just about music but a survival battle in the glitzy world of Hollywood.
What you are about to uncover might shatter the perfect image of the band you adore! 👇
That was Michael Anthony, okay? 100% dedicated. Never did anything to hurt those guys. And they tried to hurt him again and again and again. Behind Van Halen’s explosive riffs, wild stage antics, and headline making feuds, one man held it all together quietly, powerfully, and with more sacrifice than fans ever knew. But his […]
Dubai Sheikh’s $2M Wedding to Filipina Ends in Bloodbath After He Learns of Her 3 Husbands
It was supposed to be the wedding of a lifetime, a $2 million celebration of love between a powerful Dubai chic and a humble Filipina. Instead, it became a bloodbath that exposed a web of lies, betrayal, and the dark underbelly of Dubai’s marriage market. For men who believed they possessed the same woman’s heart. […]
Dubai Sheikh’s $2M Wedding to Filipina Ends in Bloodbath After He Learns of Her 3 Husbands – Part 2
He froze midstride when he saw Farid standing near Rosa. What is this? Vikram demanded, recognizing Farid from the screen. You’re one of them, one of the other husbands. Before either man could respond, Jalil Al- Elzabi entered from the western door, accompanied by two male relatives. At 63, Jal moved with the deliberate dignity […]
Sheikh’s $3M Wedding With Filipina Bride Turns Deadly After Her Ex-Boyfriend’s Secret Video – Part 4
I was praying again on my knees, head bowed, hands raised, whispering worship to Jesus. But this time, Rasheed saw something he could not explain. Light, soft, golden light surrounding me. Not from any source he could identify, not from the small window. It was the middle of the night, not from outside the cell. […]
End of content
No more pages to load